- EDR vs NDR
- EDR vs NDR
- How Does NDR Work?
- What is XDR?
- Integrating NDR

Tom Bienkowski
Senior Director, Security Product Marketing
What is Network Detection & Response (NDR)?
Network Detection and Response (NDR) serves as a comprehensive cybersecurity solution, meticulously monitoring a company's network for cyber threats and irregular activities across on-premise, public, and private cloud, as well as hybrid environments. This advanced form of cybersecurity fills potential blind spots in security visibility when integrated with complementary solutions such as log analysis tools (SIEM) and Endpoint Detection and Response (EDR), contributing to a robust cybersecurity strategy. Unlike EDR tools, which primarily concentrate on endpoints, NDR solutions deliver more holistic data coverage.
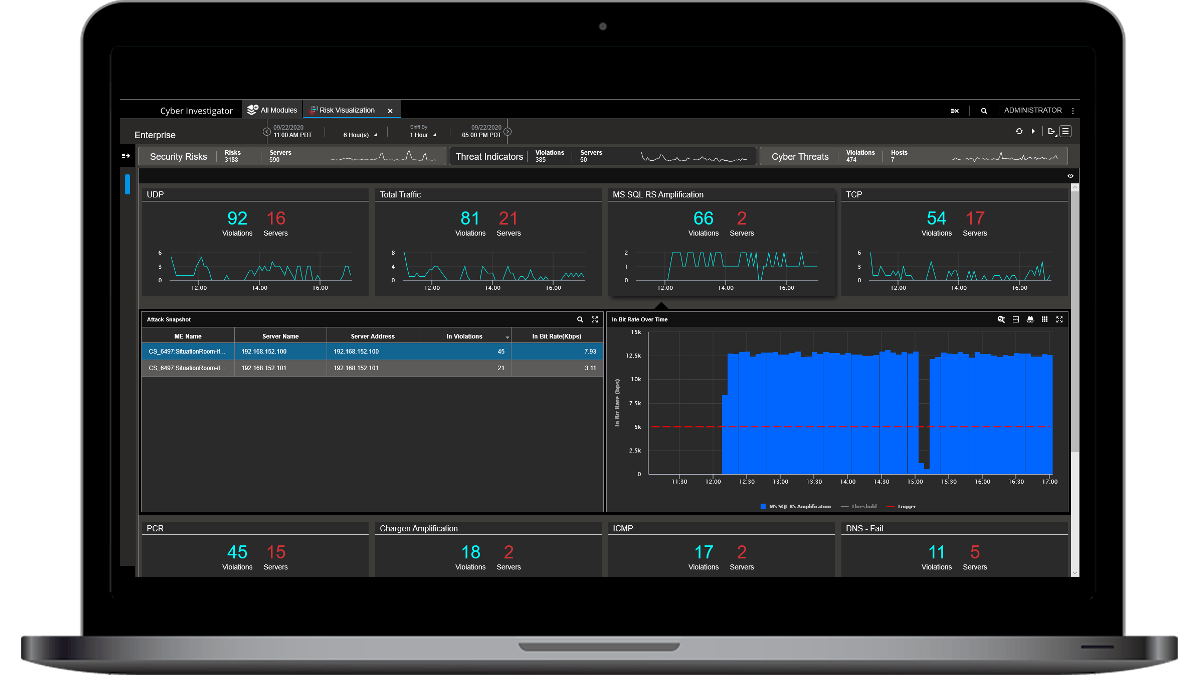
Additionally, compared to SIEMs that depend on log data that cyber attackers can tamper with, NETSCOUT Advanced NDR employs network packet data, offering a higher degree of granularity and reliability. An example of this intricate approach is Omnis Cyber Intelligence, an NDR solution designed to provide more comprehensive and detailed data for enhanced security.
As enterprises expand their IT infrastructure to enable remote workforces, leverage the cloud, and facilitate new innovations, the need for more robust cybersecurity approaches is imperative. In response to these challenges, a growing number of enterprises are relying on network detection and response (NDR) solutions to fill gaps left with existing security toolsets.
NDR toolkits heighten security capabilities by automating responses to threats, enabling security and network operations teams to collaborate more effectively, leading to better detection and mitigation. NDR cybersecurity also reduces the burden on security resources, freeing up personnel to focus on other important tasks.
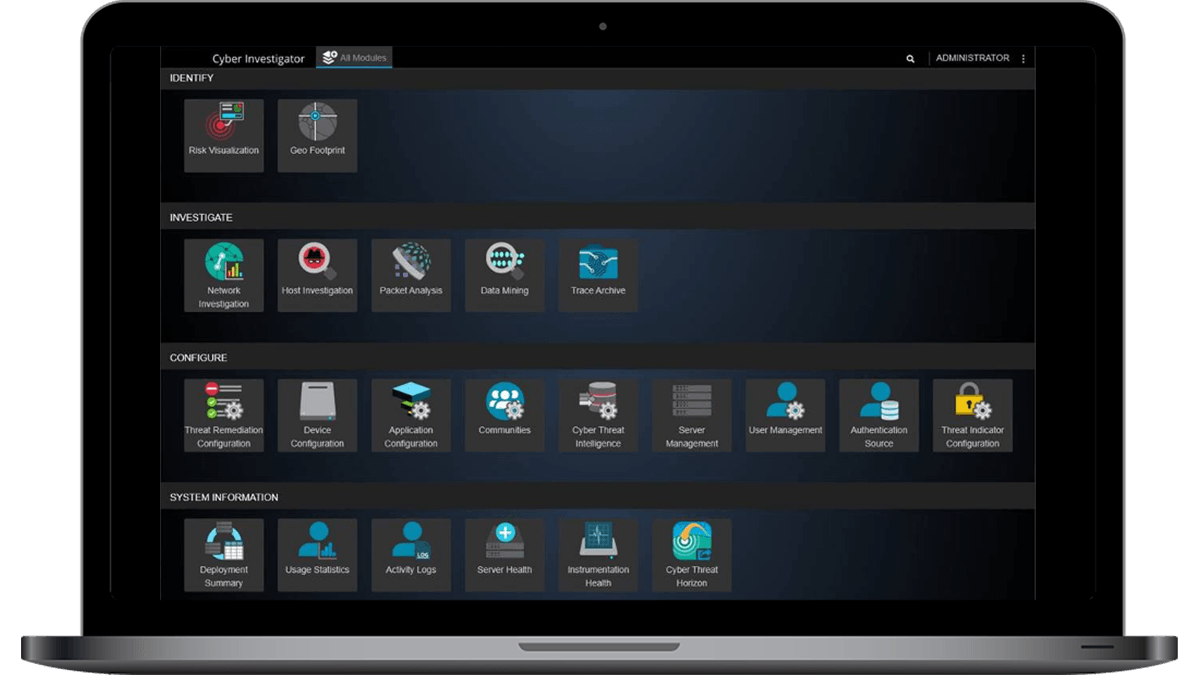
When powered by network packet data, NDR toolkits can provide real-time attack surface monitoring, early warning capabilities, contact tracing, and back-in-time analysis to locate attackers within the network. With Omnis Cyber Intelligence, NETSCOUT provides a deep packet inspection-based and cloud-native NDR toolset that helps security teams effectively respond to increased complexity, tool sprawl, false positives, and organizational silos.
What is the difference between EDR and NDR for Cybersecurity?
EDR is designed to monitor and mitigate endpoint attacks. These attacks are typically focused on endpoints in a network like computers and servers. NDR monitors network traffic in its entirety to gain visibility into potential cyberthreats, delivering real-time visibility across the broader network. These tools work well as complements to each other, though many enterprises aren’t deploying NDR solutions as effectively as they could be.
Learn About our Cybersecurity & NDR Solutions
How does Network Detection and Response work?
NDR is a security tool that monitors an enterprise’s network traffic to gain visibility into potential cyberthreats that relies on advanced capabilities, such as behavioral analytics, machine learning, and artificial intelligence to uncover threats and suspect activities. Once detected, NDR solutions take action against threats using their own capabilities, or through coordinated actions in conjunction with other cybersecurity tools.
NDR solutions work by modeling the tactics, techniques, and methodologies found in the MITRE ATT&CK framework. NDR can cut the time spent conducting investigations by leveraging high-fidelity data and comparing it to a timeline of events to reveal attack behaviors. This data can also be shared with security information event management (SIEM) solutions to create broader security assessments.
NDR solutions are highly effective at detecting threats and then taking action against these threats in real time through their own capabilities. NDR is also effective when used in support of other cybersecurity tools.

Case Study for NDR
NETSCOUT Omnis Cyber Intelligence bridges both network and security perspectives for improved Network Operations and Security Operations for a large healthcare/hospital network.
What is XDR (Extended Detection and Response)?
Extended Detection and Response (XDR) is a method of detecting and responding to threats, eliminating the challenges of traditional security silos, thus enabling the delivery of more effective protection against cyberattacks and unapproved access.
Forrester Research defines XDR as: “The evolution of EDR, which optimizes threat detection, investigation, response, and cyber threat hunting in real time. XDR unifies security-relevant endpoint detections with telemetry from security and business tools such as network analysis and visibility (NAV), email security, identity and access management, cloud security, and more. It is a cloud-native platform built on big data infrastructure to provide security teams with flexibility, scalability, and opportunities for automation.”
How do I Integrate Network Detection and Response?
NDR solutions are often used in conjunction with other security solutions as part of a more comprehensive approach.
NDR solutions can be integrated with existing systems. These solutions are designed to create little friction with SOCs, yet offer effective network threat detection. Relying on sensors implemented off a SPAN or TAP port, NDRs can passively monitor network traffic.
Integration with SIEM
SOCs can seamlessly integrate NDR solutions with SIEMs, enabling full visibility within existing workflows, while still enabling a shift into NDR as required for deeper analysis.
Integration with SOAR
Many NDR cybersecurity integrations occur within large enterprises with mature SOCs who prefer to leverage their own playbooks and workflows for a response. Therefore, many NDR vendors provide integration with security orchestration automation and response (SOAR) tools from vendors such as Splunk, Palo Alto Networks, and Swimlane.
Integration with workloads in public or private clouds
With many enterprises moving data and workloads to the cloud, integrating NDR capabilities across cloud and hybrid-cloud environments makes a lot of sense. Such integration enables the monitoring of network traffic through the different domains, providing comprehensive coverage and protection.
NETSCOUT’s Network Detection & Response Solution
For more than two decades, NETSCOUT has managed the world’s most complex networks using a patented technology called Adaptive Service Intelligence (ASI). ASI technology converts raw packets into a robust set of Layer 2-7 metadata in real-time that can be used for network/application performance analysis and cybersecurity user cases such as:
Advanced Early Warning
- Real-time detection of all suspicious network activity
Continuous Attack Surface Monitoring
- Comprehensive and real-time attack surface visibility
Contact Tracing
- Ability to track the lateral movement of an attacker
Back in Time Investigation
- Complete retrospective analysis of incidents
