Decrypt SSL/TLS Encrypted Traffic for High Performance Active and Passive Assurance Tools
The nGenius Decryption Appliance (nDA) enables high-performance visibility into traffic encrypted with TLS/SSL and SSH (including the latest standards). With active inline and passive out-of-band deployment options, nDA can support up to 40Gbs of bi-directional traffic while assuring optimal performance of downstream service and security assurance tools.
Purpose Built and High Performing
Experience the NETSCOUT Advantage
nGenius Decryption Appliance is a purpose-built, high-performance TLS & SSL decryption tool for the most demanding, pervasive security monitoring applications. When security-optimized capabilities and value really matter, enterprises and service providers alike select NETSCOUT.
NETSCOUT products are used by over 20,000 enterprise customers, including 92 of the Fortune 100 and more than 150 top service provider customers. nGenius Decryption Appliance integrates seamlessly with the NETSCOUT nGenius Packet Flow Switches or any 3rd party packet brokers and is supported by the company’s business processes, including its award-winning customer care program.
Assure Optimal Performance
Optimized for Security
Remove security blind spots with nDA and gain visibility into encrypted traffic with full crypto support.
Maintain end-to-end security posture and send clear traffic to one or more security monitoring tools without the need for multiple decryption steps.
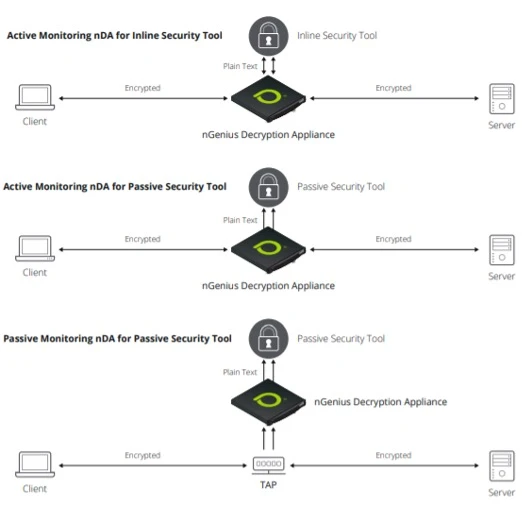
Active and Passive Security Monitoring
Deploy in a passive (out-of-band) or active (inline) tool-chaining configuration and place your security monitoring systems in a customizable virtual chain.
Reduce the port requirement by 50 percent, freeing up ports to connect more systems. Each system in the chain receives only the traffic of interest, increasing efficiency.
Hardware-Accelerated Performance
Purpose-built decryption acceleration hardware enables line rate processing free from bottlenecks.
High-performance packet processing resource provides hardware acceleration where the TLS and SSL decryption functions are performed to extend limits on throughput and prevent variable latency.
Data Privacy and Compliance
Comprehensive policy management functionality enables flexible policy-based decryption within your TLS and SSL decryption tools.
Maintain end-to-end security without degrading your security postures.
Optimized for Security
Optimized for Security
Optimized for Security
Remove security blind spots with nDA and gain visibility into encrypted traffic with full crypto support.
Maintain end-to-end security posture and send clear traffic to one or more security monitoring tools without the need for multiple decryption steps.
Active and Passive Security Monitoring
Active and Passive Security Monitoring
Active and Passive Security Monitoring
Deploy in a passive (out-of-band) or active (inline) tool-chaining configuration and place your security monitoring systems in a customizable virtual chain.
Reduce the port requirement by 50 percent, freeing up ports to connect more systems. Each system in the chain receives only the traffic of interest, increasing efficiency.
Hardware-Accelerated Performance
Hardware-Accelerated Performance
Hardware-Accelerated Performance
Purpose-built decryption acceleration hardware enables line rate processing free from bottlenecks.
High-performance packet processing resource provides hardware acceleration where the TLS and SSL decryption functions are performed to extend limits on throughput and prevent variable latency.
Data Privacy and Compliance
Data Privacy and Compliance
Data Privacy and Compliance
Comprehensive policy management functionality enables flexible policy-based decryption within your TLS and SSL decryption tools.
Maintain end-to-end security without degrading your security postures.
Resources
Related Pages
With speeds ranging from 1Gbps to 400Gbps, nGenius 7000 Series Packet Flow Switches provide core packet broker functionality as well as filtering, load balancing, and more.
The nGeniusONE® solution provides observability into any infrastructure environment - data center, private & public cloud, remote offices, and co-locations.
Faster, Smarter Incident Response Starts with the Right Data.

Contact NETSCOUT Today
To learn more about how NETSCOUT can help your company, speak to one of our highly experienced subject matter experts.

