NETSCOUT Knows Government
Unlike commercial enterprises, when government agencies fail to meet and overcome challenges, citizens and residents are impacted which too often can have life changing consequences. As agencies embark on digital transformation, tool consolidation, shared services and 5G technology refreshment, NETSCOUT observability can help. Our solutions are backed by key government certifications, more than 35 years of technology expertise, and a best-in-class partner ecosystem committed to your success when addressing zero trust architectures, cybersecurity threats, cloud migration, application performance and network availability–everything you need to be unstoppable.
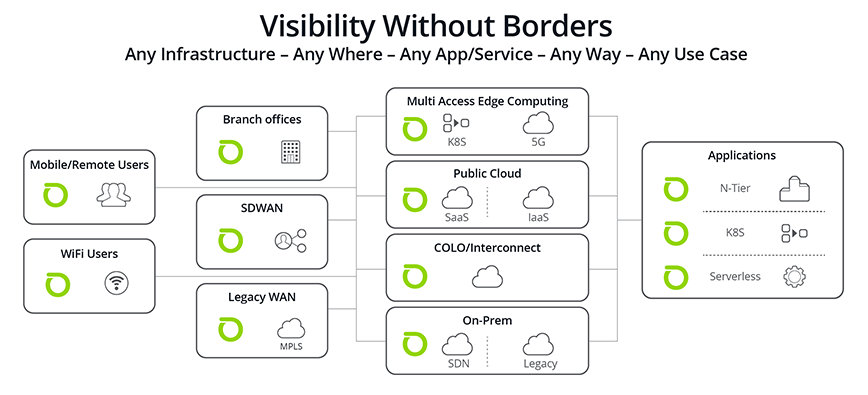
We are the market leader in DDoS protection and service assurance. Our Visibility Without Borders strategy aligns to support your strategic technology initiatives. We leverage what we learn from our Enterprise and Service Provider customers to empower you, our government customers.
We Can Help
As you continue to drive digital transformation to better serve the mission, your constituents, citizens or residents, we can help. We’ve helped our government customers with:

Department of Defense & Intelligence Agencies
Learn how we support the DoD & Intel Agencies as they modernize, accelerate enterprise Cloud adoption and deployment and aggressively defend DoD missions from disruption by cyber-attacks.

Federal Civilian Agencies
Explore how NETSCOUT is helping Civilian Agencies keep their networks and applications running and protected from disruptions with NETSCOUT Smart Data Technology.

State & Local Governments
See how State and Local Governments benefit from Visibility Without Borders to serve their residents and provide the critical services they need to stay safe and secure.

Certifications & Accreditations
Discover how NETSCOUT ensures our flagship products meet the high standards of security and reliability required for agency procurement pathways and partners.

Partners & Alliances
Learn more about strategic our partnerships with technology leaders NETSCOUT’s partner ecosystem enhances our customers’ ability to thrive and win in the face of daunting challenges and massive complexity.

Government Success Stories
Discover more examples of government agencies utilizing NETSCOUT solutions to solve some very tough problems, overcome difficult challenges and better support the people they are sworn to protect, provide for and serve.
