Rethinking DDoS Defenses
Comprehensive, dynamic DDoS protection is critical for combating adaptive DDoS attacks.

The other night I rented a movie called “The Biggest Little Farm.” The movie depicted a couple who were new to farming but attempting to regenerate a farm that had fallen into disrepair. In the process, they continually ran into challenges regarding how to protect the crops and animals on the farm. Initially, they brought in goats to eat some of the overgrown vegetation, which in turn attracted the initial threat, which was coyotes, who were killing the goats and some of their chickens, so they put up a fence. Then birds of prey became a threat, so the farmers installed roofs on the cages. Then it was rabbits and gophers eating the vegetables, and so on. Each time they encountered a new challenge, the farmers had to adapt and build a new defense. In some cases, they didn’t know what was coming next or how to fight it, so they talked to neighbors to understand how they did it. I started thinking that although this was taking place on a farm, it was the typical approach to perimeter protection whether on a farm, a castle, a fort, or—in today’s world—your network.
This movie was particularly thought-provoking to me as I began reading the current NETSCOUT DDoS Threat Intelligence Report in preparation for a project regarding today’s networks and how customers manage DDoS attacks. The report highlights the fact that distributed denial-of-service (DDoS) attacks are again evolving. This year, reflection/amplification attacks, which have been the preferred attack vector over the past couple of years, took a back seat to TCP state exhaustion attacks. What this indicates is that the bad actors are attempting to execute attacks that are increasingly difficult to detect because they mimic legitimate traffic and require defenders to have some level of expertise and technology to recognize them as attacks.

Watch to learn more on detecting and mitigating state exhaustion DDoS attacks.
Adaptive DDoS Attacks on the Rise
The threat report also reveals that one of the ways attackers are becoming more effective in the destruction of network availability is by using adaptive DDoS. In an adaptive DDoS attack, adversaries perform extensive pre-attack reconnaissance to identify specific elements of the service delivery chain to target—for example, state exhaustion attacks, which made up four of the top five attack vectors this year, target stateful devices that are an integral part of the security stack such as firewalls and VPN concentrators. These targets are attractive because the attacks against them can be smaller in size and designed to evade defenses meant for other threats. Think of the fence designed for the coyotes that won’t stop weasels because the openings are too big. These types of preparations are calculated to minimize the number of administrative boundaries; DDoS attack traffic must traverse, often resulting in fewer opportunities to detect and mitigate the attack. Figure 1 lists some of the characteristics of adaptive DDoS attacks.
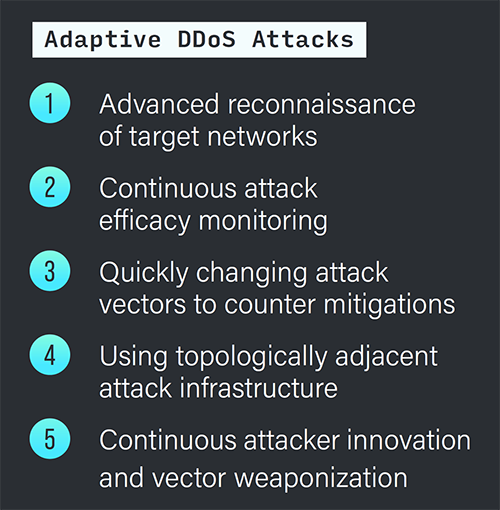
Figure 1: Five characteristics of adaptive DDoS attacks
Because of these advances in attack methods, network operators must adapt their defenses to meet the new challenges. In our experience, and primarily due to the nature of ever-changing attacks, the required defense needs to be able to not only manage volumetric attacks but also identify the many attacks that currently are designed to elude known defense measures. And in most cases, this is not a situation where there is a one-size-fits-all solution. As in “The Biggest Little Farm,” the ever-changing threat landscape we are currently experiencing requires an agile defense model—in this case, one that works inside and outside the network and adapts to changing attack vectors and methods.
Why You Need a Hybrid Defense Strategy
The best practice for protecting your network in today’s ever-changing DDoS attack landscape is a hybrid approach. Protection strategies of the past will suffice in some situations, such as in an attack designed to overwhelm your internet circuit before traffic arrives on your site. However, attacks specifically designed to evade those protections, such as TCP state exhaustion and application-layer attacks, are the basis for the new attack landscape. Furthermore, the ability to respond quickly to attacks that dodge the cloud solution and hit the network edge or an internet-facing service is imperative, and having the agility to change defenses rapidly to adapt to subtle changes in adaptive DDoS onsite is crucial.

By implementing adaptive DDoS defenses such as NETSCOUT’s Omnis Adaptive Edge Defense (AED) at all edges of their networks, network operators can overpower DDoS attack traffic as it enters the network edge—or before it ever unites into a large-scale attack. With edge-based attack detection combined with cloud-scrubbing capacity, automated bilayer communication, indicators of compromise (IoC) analysis, command-and-control (C2) communication blocking, and current actionable threat intelligence (think of the farmers talking to their neighbors), operators can tackle any DDoS attack before it can cause damage (see Figure 2).
As the movie ended, the farmers were getting management of the constantly evolving threats nature could throw at them under control. The underlying reason for that control was that they began to understand the developing threats and were proactive in their actions to block them. This could be a valuable lesson in our approach to new methods behind DDoS attacks.
For more information on hybrid, dynamic, comprehensive DDoS protection, download the white paper “An On-Premises Defense Is the Cornerstone for Multilayer DDoS Protection.”