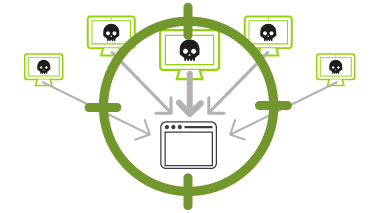
Why is a DDoS attack dangerous?
DDoS represents a significant threat to business continuity. As organizations have grown more dependent on the Internet and web-based applications and services, availability has become as essential as electricity.
DDoS is not only a threat to retailers, financial services and gaming companies with an obvious need for availability. DDoS attacks also target the mission critical business applications that your organization relies on to manage daily operations, such as email, salesforce automation, CRM and many others.
Additionally, other industries, such as manufacturing, pharma and healthcare, have internal web properties that the supply chain and other business partners rely on for daily business operations. All of these are targets for today’s sophisticated cyber attackers.

What are the consequences of a successful DDoS attack?
When a public facing website or application is unavailable, that can lead to angry customers, lost revenue and brand damage. When business critical applications become unavailable, operations and productivity grind to a halt. Internal websites that partners rely on means supply chain and production disruption.
A successful DDoS campaign also means that your organization has invited more attacks. You can expect attacks to continue until more robust DDoS defenses are deployed.
Learn What Proper DDoS Defense Means

Can Firewalls, Intrusion Detection/Protection Systems, Application Delivery Controllers / Load Balancers prevent a DDoS Attack?
IPS devices, firewalls and other security products are essential elements of a layered-defense strategy, but they are designed to solve security problems that are fundamentally different from dedicated DDoS detection and mitigation products. IPS devices, for example, block break-in attempts that cause data theft. Meanwhile, a firewall acts as policy enforcer to prevent unauthorized access to data.
While such security products effectively address “network integrity and confidentiality,” they fail to address a fundamental concern regarding DDoS attacks—”network availability.” What’s more, IPS devices and firewalls are stateful, inline solutions, meaning they are vulnerable to DDoS attacks and often become the targets themselves.
Similar to IDS/IPS and firewalls, ADCs and load balancers have no broader network traffic visibility nor integrated threat intelligence and they are also stateful devices vulnerable state-exhausting attacks. The increase in state-exhausting volumetric threats and blended application-level attacks, makes ADC’s and load balancers a limited and partial solution for customers requiring best-of‐breed DDoS protection.
Can Content Delivery Networks (CDN) prevent a DDoS Attack?
The truth is a CDN addresses the symptoms of a DDoS attack by simply absorbing these large volumes of data. It lets all the information in and through. All are welcome. There are three caveats here. The first is that there must be bandwidth available to absorb this high-volume traffic, and some of these volumetric-based attacks are exceeding 300 Gbps, and there is a price for all the capacity capability. Second, there are ways around the CDN. Not every webpage or asset will utilize the CDN. Third, a CDN cannot protect from a non-Application-based attack like a UDP or TCP state exhaustion attack. So let the CDN do what it was intended to.

Can a Web Application Firewall (WAF) prevent a DDoS Attack?
A WAF is a stateful pack processing device designed to stop web-based application attacks and therefore does not stop all DDoS attack types such as TCP-state exhaustion attacks. Any sort of reflection or amplification flooding attack using numerous sources would overwhelm a WAF rendering the entire solution useless. The bottom line is that these two technologies (WAF and CDN) are complementary in their use to protect organizations from attack, but a WAF will not protect from the extensive vectors of DDoS attacks.
What is NETSCOUT’s Approach to DDoS Protection?
NETSCOUT's Arbor DDoS protection solution has been protecting the world’s largest and most demanding networks from DDoS attacks for more than a decade. We strongly believe that the best way to protect your resources from modern DDoS attacks is by means of a multi-layer deployment of purpose-built DDoS mitigation solutions.
Only with a tightly integrated, multi-layer defense can you adequately protect your organization from the full spectrum of DDoS attacks.
- Arbor Cloud (Tightly integrated, cloud-based, multi-layer DDoS protection)
- Arbor Edge Defense (On-Premises)
- Arbor Sightline/Threat Mitigation System (High Capacity On-Premise Solution for Large Organizations)
NETSCOUT customers enjoy a considerable competitive advantage by getting both a micro view of their own network, via our products, combined with a macro view of global Internet traffic, via NETSCOUT Cyber Threat Horizon, an interface to our ATLAS threat intelligence and a DDoS Attack Map visualization.
