- DDoS
- Arbor Networks - DDoS Experts
Measuring the Cruellest Month
DDoS Attacks During a Pandemic

Summary
One of the more esoteric aspects of working in the DDoS defense space is the analysis of data. We look at data about attack bandwidth (bps) and throughput (pps); connections per second (cps) and queries per second (qps); source and destination CIDRs and ASNs; mitigation capacities and attack vectors; geographies and market sectors; and many other quantifiable aspects of the trade. There’s always a high degree of interest in the overall trajectory of attack volume and frequency (mostly up and to the right, with occasional valleys in amongst the peaks) over the course of a given month, or quarter, or year.
Data of this nature are very important to network operators, because it helps them understand changes in the overall internet threat milieu, which can affect their organization’s security posture and inform their planning and decision-making with regards to DDoS response plans, capabilities, and infrastructure. Internet Service Providers (ISPs) and enterprises alike know that having insight into both current characteristics and the anticipated evolution of threats to network and service availability is vital to maintaining and defending their public-facing internet properties, even in the face of attack.
At NETSCOUT, our sensorium includes internet-wide visibility into DDoS attacks via a wide variety of tools:
- Our ATLAS anonymized attack statistics collection and sharing platform, as well as DDoS honeynets
- Our internet Albedo initiative to quantify and monitor DDoS reflectors/amplifiers on a global basis
- Disassembly and analysis of malware and DDoS attack tools
- Infiltration and monitoring of botnet command-and-control (C&C) networks
- Ongoing identification and study of new DDoS attack vectors, along with mechanisms to detect and classify them and successful mitigation countermeasures and defense techniques.
Consequently, we have an extremely broad data horizon, which affords a unique perspective on DDoS attack activity across the internet as a whole. We’re often able to identify the debut and weaponization of new DDoS attack vectors as well as anticipate trends in attack prevalence and, in some circumstances, discern likely attacker motivations.
Anticipating and appraising the impact of global events such as the COVID-19 pandemic on the internet threat landscape is an important aspect of our work, as it allows us to keep our customers and partners abreast of important developments that can potentially impact their online security environments. It also informs our ongoing development of new defense capabilities for NETSCOUT’s Arbor DDoS visibility and mitigation solutions. And sometimes, looking at DDoS attack data from a different perspective unveils new insights into the interrelationships between the online and physical worlds, and allows us to better assess their mutual impact upon one another and on society as a whole.
Key Findings
- DDoS attack count, bandwidth, and throughput all saw significant increases since the start of the global COVID-19 pandemic.
- Wired and wireless broadband access networks took the brunt of attacks, as the vast majority of the increased traffic relates to gaming and gambling in relation to gaming.
- Despite the massive increases in overall traffic across the entire internet and the large increase in DDoS Attacks, service operators and ISPs have risen to the challenge and performed an amazing feat to maintain access continuity and provide the much-needed critical Infrastructure for businesses and consumers alike.
- The constant global toll of DDoS attacks in aggregate is significant and must be analyzed in detail.
By the Numbers
Once widespread quarantine orders went into effect, many network operators worldwide reported significant increases in customer traffic, much of it due to greatly expanded use of video-capable conferencing applications such as Zoom, WebEx, Skype, FaceTime, Google Duo, Hangouts, and Slack, by large numbers of new remote workers.
- In the Asia Pacific (APAC) region, some ISPs increased their peering and core bandwidth capacities more than they’d planned for the entire calendar year, all in the span of a few weeks; and operators of some popular conferencing systems worked feverishly to install more hardware and provision more peering and transit bandwidth to support the flood of new users.
- DNS operators across the board reported a ~25% qps increase for both recursive and authoritative DNS servers, with a flood of queries for internal-only private domains directed towards their DNS infrastructure by office computers that have been taken home for use by remote workers.
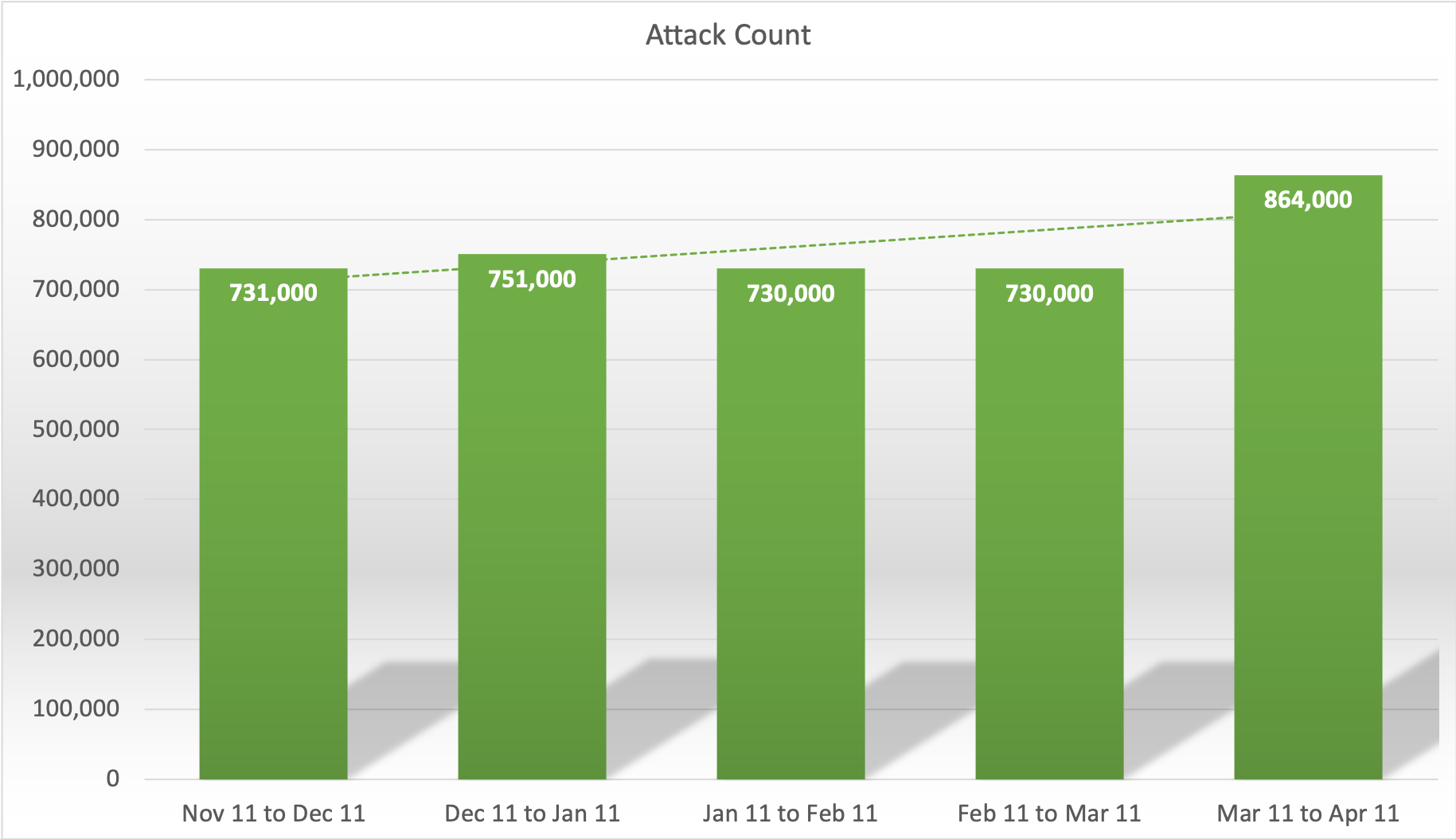
- From November 11th of 2019 – March 11th of 2020, NETSCOUT Arbor observed an average of ~735,000 DDoS attacks/month, with a peak of ~751,000 during the December holiday period. But from March 11th – April 11th of 2020, we observed more than ~864,000 DDoS attacks (Figure 1), the single largest number of attacks we’ve seen over any other 31-day period to date, and a 17% increase over the previous peak for an equivalent interval.
- The above DDoS attack numbers are derived from our ATLAS database and made available via NETSCOUT's Cyber Threat Horizon.
The most frequently cited statistics related to DDoS attacks tend to be the below mentioned bps and pps; network operators and the industry press take note for a few days when new attack thresholds are reached, and it makes news for a few days or weeks, until the next high-water mark is reached. Though some notable DDoS attacks have exhibited durations of months or even years, most individual attacks last for minutes or hours; concerted attack campaigns can go on for weeks or longer. It’s therefore important to record the progression of attack volumes for DDoS mitigation planning purposes.
And while we did observe another terabit-class attack during this period, we don’t believe this to be the most significant DDoS-related metric during this interlude. That honor goes to the sheer amount of bandwidth and throughput consumed by DDoS attacks in toto, an extremely revealing number. In fact, we don’t recall seeing DDoS attack statistics of this nature being publicly made available, until now.
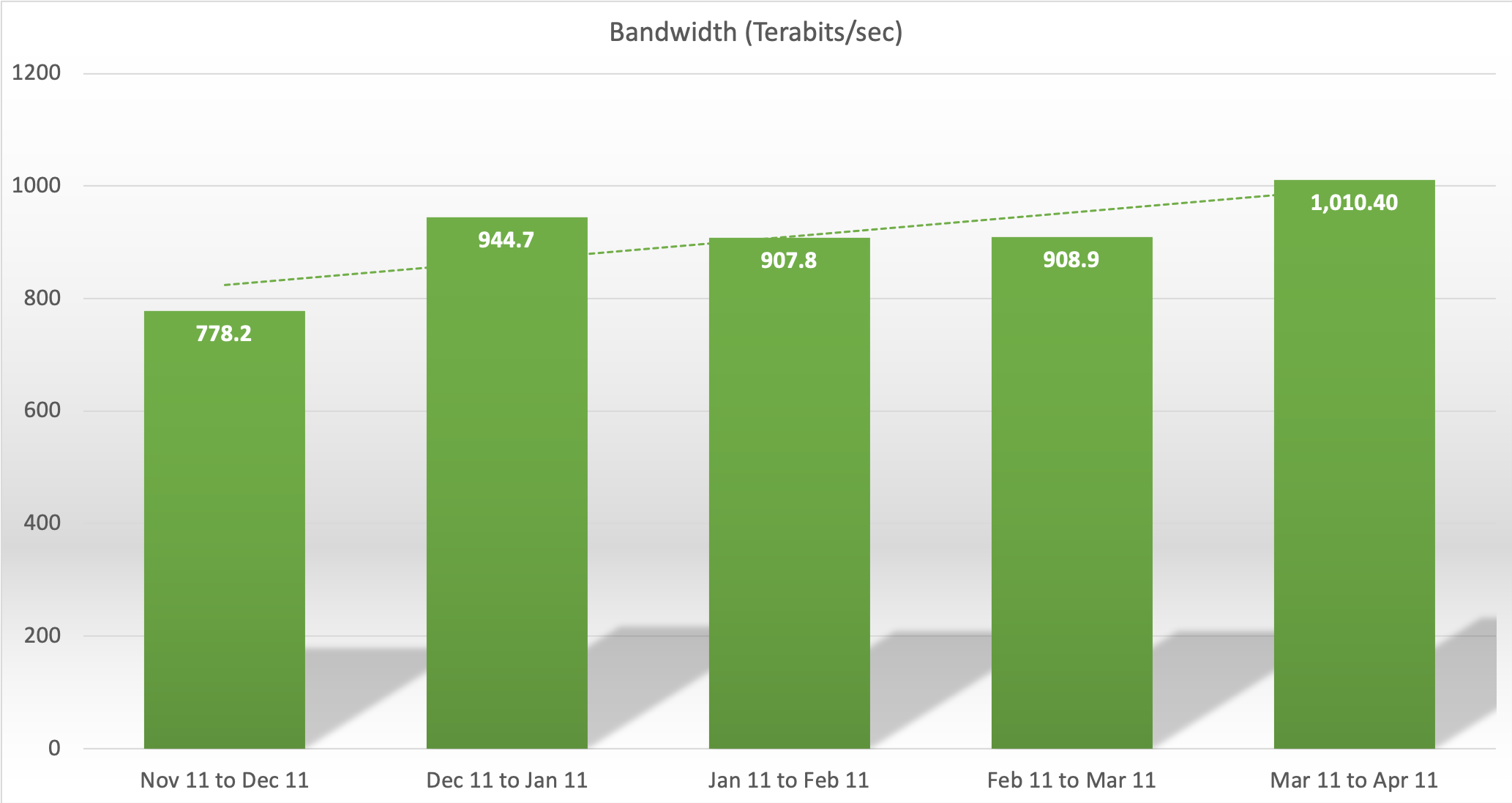
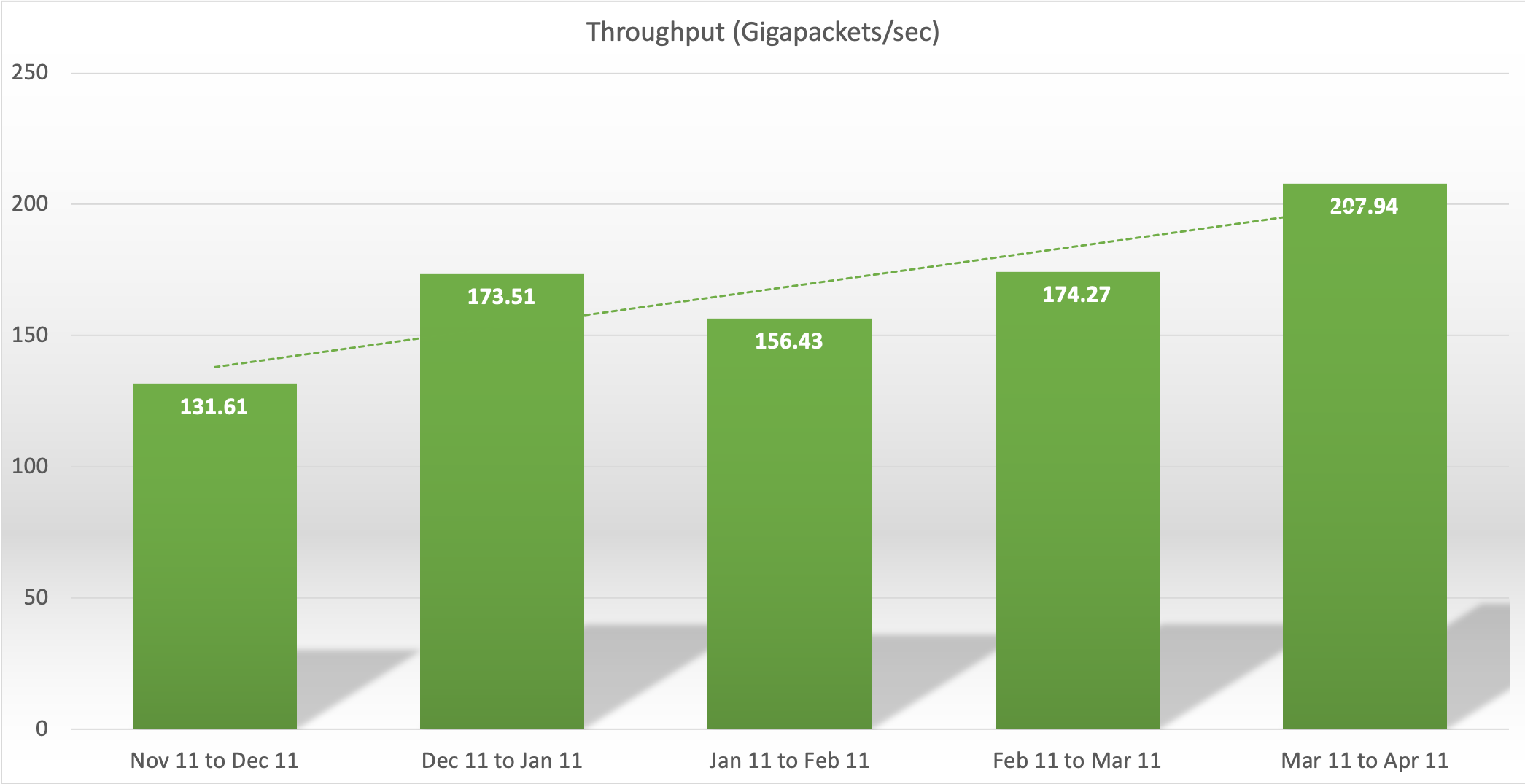
Going back to November 11th of 2019, if we combine the aggregate bps and pps of all observed DDoS attacks from that day through March 11th of 2020, we derive a monthly average of ~885 tbps and ~159 gigapackets/sec (gpps), respectively. And while there are methods to calculate how much the average DDoS attack costs its target(s) in terms of CAPEX and OPEX on a per-incident basis, the sheer magnitude of DDoS attack traffic that takes place on an ongoing basis represents an enormous, untold, and seemingly perpetual tax on every internet-connected organization and individual across the globe.
For the critical period between March 11th and April 11th, 2020, we observed a whopping ~1.01 pbps and ~208 gpps of aggregate DDoS attack traffic during the post-quarantine surge. This represents a non-trivial 14% increase in attack bps (Figure 2) and a staggering ~31% increase in attack pps (Figure 3), respectively.
Just pause for a moment and think about the import of these remarkable aggregate DDoS attack traffic statistics. While DDoS defense is our forte, and while we constantly work with our customers and the global operational community as a whole to detect, classify, and mitigate the largest and most complex DDoS attacks on the internet, we found that quantifying the sheer scale of the constant barrage of DDoS attacks across the internet as a whole to be truly stunning—especially in light of the fact that attacks related to online gaming increased so dramatically during events of such serious societal import. The implications are quite sobering, to say the least.
DDoS Targets of Interest
Speaking of online gaming, one of our first thoughts when we learned of the pandemic-related self-quarantine and social distancing policies being enacted globally was that DDoS attacks would likely increase in frequency and impact in the near term. Why? The answer is simple: quarantines mean widespread school closures. And closed schools invariably lead to a surge in DDoS attacks, as evidenced by the seasonal increases in DDoS attacks numbers we routinely observe during major holidays. As we predicted, a surge in DDoS attacks greater than that normally observed during school holiday seasons began contemporaneously with the announcement of self-quarantine measures going into effect across large jurisdictions. And there’s one reason: online gaming.
Within the operational security community, it’s common knowledge that close to 90% of all DDoS attacks across the entire internet are primarily motivated by rivalries, disputes, and organized illegal gambling activities directly related to online gaming. That’s right—by the numbers, the vast majority of DDoS attacks, and a non-trivial proportion of the defense-related CAPEX and OPEX investments network operators are forced to make, are a side effect of conflicts that can most charitably be described as highly . . . abstract.
Like clockwork, general increases in the frequency of DDoS attacks tend to occur during summer and winter breaks for middle schools, high schools, colleges, and universities. And also, like clockwork, those numbers tend to decline (with occasional spikes tied to exam schedules) when schools are called back into session. However, the decline rarely matches the magnitude of the increase, with the result that overall DDoS attack numbers and impact have steadily ratcheted upwards over time.
This isn’t meant to imply that DDoS attacks motivated by criminal extortion, ideology, geopolitical conflicts, and other factors are trivial—far from it! Some of the largest, most complex, and highest-impact DDoS attacks stem from these far more serious motivations. But by the numbers, online gaming has led the pack in terms of inspiring DDoS attacks for many years, and we don’t anticipate that changing anytime soon.
It would be logical to assume that most gaming-related DDoS attacks would tend to target the online presence and infrastructure of popular gaming developers and distributors. While attacks of this type do occur, it appears that most gaming-related DDoS attacks actually target wireline and wireless consumer broadband access networks—that is, the “eyeball” networks we all use at home (and sometimes at work) to surf the Web, post cat pictures, chat with friends and acquaintances, and, yes, play those selfsame video games. Via various means such as sniffing network traffic from the games themselves and/or out-of-band voice over IP (VoIP) systems used by game players to chat, attackers can often identify the IP address of other players due to the peer-to-peer nature of those games and VoIP systems, and then make use of booter/stresser services to launch DDoS attacks against them directly.
This means that broadband access networks disproportionately bear the brunt of many gaming-related DDoS attacks, and that the vast majority of attacks against those networks appear to result from intra-gaming disputes or illicit gambling activity surrounding game matches. While attackers can and do make use of a wide variety of DDoS attack vectors, the most common attack methodologies to date are various UDP reflection/amplification attacks, making use of abusable DNS, ntp, C-LDAP, et. al. reflectors/amplifiers. More recently, TCP reflection/amplification attacks have grown in popularity, along with carpet-bombing target addressing for both UDP and TCP reflection/amplification attacks. This has coincided with the weaponization of these attack vectors and targeting methodologies, making them accessible to relatively unsophisticated attackers.
Unseen Heroes of the Internet
It is important to recognize that while there have been anecdotal reports of internet slowdowns and episodic unavailability of some popular services and applications since the official start of the CoVID-19 pandemic, it is apparent that network and service operators as a whole have stepped up to the challenge and performed a remarkable feat of operational continuity under extremely trying circumstances. In particular, broadband access network operators have done so while simultaneously defending against an unprecedented surge in both frequency and aggregate volume of DDoS attacks targeting their networks and customers. At a time when the internet as a whole unquestionably meets the textbook definition of critical infrastructure, this signal achievement should be recognized and emulated in the crucial weeks and months to come.
Conclusion
Once the tactical challenge of maintaining availability during this period of unprecedented strain on the worldwide internet infrastructure has been met, it is imperative that network operators, researchers, vendors, and regulators alike work together to quantify the true ongoing costs of DDoS attacks across the internet as a whole. By doing so, we can provide a much-needed impetus for efforts to implement industry best current practices as broadly as possible to reduce the overall DDoS attack surface, while at the same time ensuring that DDoS defense preparedness is recognized as an indispensable requirement for maintaining social, economic, and governmental continuity in the modern age.
- Attacks and DDoS Attacks
- Arbor Networks - DDoS Experts

