Are Attacks Hiding in Your Encrypted Traffic?
Protect your network with efficient, secure decryption and attack analysis.

Distributed denial-of-service (DDoS) attackers are both persistent and creative. One of their creative methods that has seen an increase recently is attacks on HTTPS web applications and services by employing encrypted traffic. Attackers are unrelenting in their assaults on high-value encrypted targets. The high volumes of encrypted internet traffic that traverse networks without being inspected due to the lack of efficient decryption technology make it easy for malicious actors to hide among legitimate traffic. Therefore, a key component of a security arsenal is the ability to decrypt and inspect encrypted traffic securely and attest to its authenticity without slowing, disrupting, or compromising legitimate traffic.
DDoS attacks targeting encrypted services tend to fall into four categories:
- Attacks that target the Secure Sockets Layer/Transport Layer Security (SSL/TLS) negotiation, commonly known as the “handshake,” which determines how two parties to an internet connection will encrypt their communications
- Protocol or connection attacks against SSL service ports, which seek to exploit SSL vulnerabilities
- Volumetric attacks targeting SSL/TLS service ports, which overwhelm port capacity with high-volume traffic floods
- Application-layer attacks against underlying services running over SSL/TLS
Other types of cyberattacks that employ encrypted traffic typically start with reconnaissance and an initial compromise of an endpoint or asset exposed to the internet. Once inside, attackers perform lateral propagation, including the establishment of a network foothold. Finally, attackers act to achieve their objectives, which often involve data exfiltration via malware.
What’s at Risk
Reputational and brand damage are frequently cited as one of the worst consequences of a DDoS attack due to the difficulty of calculating the damage and the understanding that it is most likely immense. Additionally, harm to an organization because of compromised secure services that employ encrypted security, such as banking or online purchases that consumers have come to trust and rely upon every day with hardly a second thought, are also difficult to validate in both monetary and reputation loss. Institutions need to take measures that go beyond encryption to ensure the integrity and availability of their most critical services and the continued credibility of their reputation and brand.
Another area of concern regarding decrypting and scanning packets is where the decryption is executed. Many organizations do not want their traffic being decrypted off-site or by a cloud service because it may require sharing private certificates with the cloud provider, which is a security risk that many enterprises aren’t willing to take. In some situations, cloud providers themselves don’t want to be responsible for managing private keys and the associated liability risks if the keys are leaked or exposed from their systems.
While decryption is not always necessary for successful mitigation, there is clearly a growing need for scalable solutions for decrypting packets that will expose malicious traffic.
TLS encryption is the primary encryption used by networks for security reasons. TLS 1.3 is one of the most popular versions being used. Decrypting TLS 1.3 traffic requires a proxy solution, and proxy solutions introduce challenges to decryption performance. For this reason, among others, encrypted traffic within application layer sessions (HTTPS) is less likely to be inspected by security products. This lack of inspection makes encrypted DDoS attacks harder to detect. The problem is that decryption is computationally expensive, so unless you have some level of filtering to identify legitimate traffic that can reduce the amount of traffic requiring decryption, it can quickly overwhelm the limited decryption capacity of a security system.
The NETSCOUT Solution
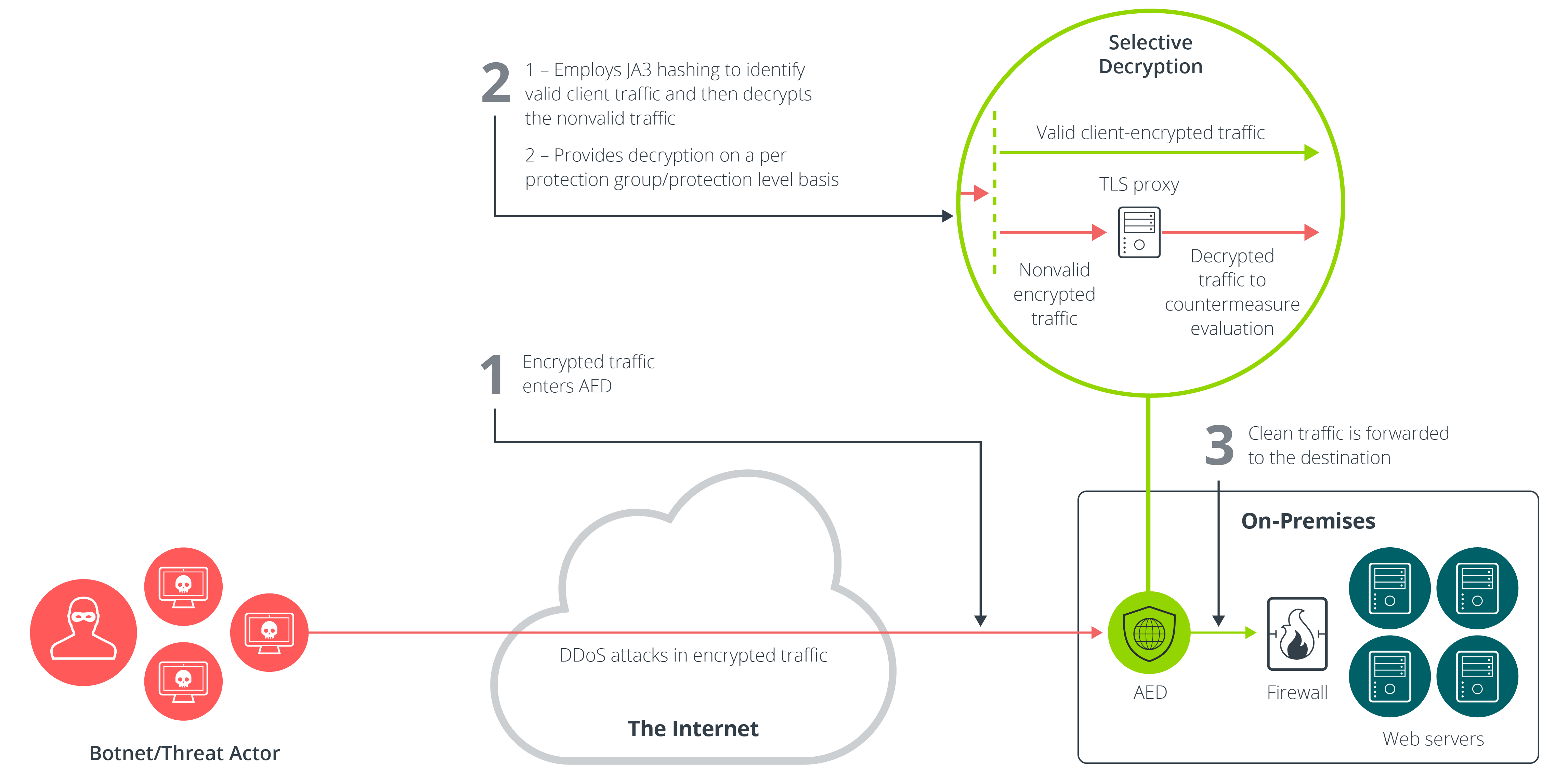
NETSCOUT’s Arbor Edge Defense (AED) 8100 sits on your network edge and intelligently determines what traffic to decrypt and what not to. As the traffic enters, AED employs JA3 hashing to identify valid client traffic and pass it on without requiring decryption. The remaining nonvalidated client traffic is decrypted and run through DDoS and other cyberattack countermeasure evaluations to identify and mitigate any malicious traffic. AED also allows users to enable decryption for a protected service and/or protection level. This allows focusing decryption only on traffic that requires it while also avoiding the unnecessary work of decrypting traffic for services that are not under attack. These features increase decryption efficiency and protect your network effectively, at scale, from attacks within encrypted traffic.
Learn more about selective decryption with NETSCOUT.