As Connectivity Grows, So Do the Risks
In our rapidly changing digital world, we rely on constant connectivity to access the tools we need to work and live. This broad online expanse provides an ever-increasing attack surface for threats that can come from nearly any direction—and a valuable opportunity for bad actors to discover and exploit new weaknesses.
This is where the NETSCOUT Omnis™ IDS solution can help. A sophisticated, high-performance intrusion detection system for enterprises of all sizes, Omnis™ IDS is comprised of Omnis™ Cyber Intelligence and Omnis™ IDS Sensor. This enterprise IDS solution provides a highly reliable, open-source system for your environment to quickly detect threats and respond in combination with NETSCOUT's broader network security portfolio.
Smarter Detection for Complex Environments
Improved IDS Usability, Visibility, and Analysis
NETSCOUT has designed Omnis™ IDS with a rich set of features that dramatically improve IDS usability, including an intuitive user interface, contextual analysis, sensor health metrics, and automated data export to other security platforms.
Omnis IDS scales from modest installations to some of the largest and most complex compute environments. It offers broad and consistent scope by using network packet data to provide true application-level, contextual visibility across all infrastructures.
![CS-00028-EN-2203-[WEB].svg](/sites/default/files/2022-04/21/images/CS-00028-EN-2203-%5BWEB%5D.svg)
Network Instrumentation
Omnis™ IDS Sensor provides comprehensive, scalable visibility into network packets throughout the environment. Omnis™ IDS Sensor leverages Suricata and supports open-source, commercial, private, and customized rulesets for high-performance threat detection.
Omnis IDS Sensor for highly scalable, open-source, smart visibility into your digital infrastructure.

Centralized Analysis and Visualization
IDS Explorer in Omnis Cyber Intelligence delivers powerful analytics and centralized management for further analysis and alert triggers by leveraging security threat events and alerts from Omnis™ IDS Sensors.
Enterprise IDS Explorer in Omnis Cyber Intelligence for powerful analytics and centralized management via intuitive Web UI.

Seamless Integration
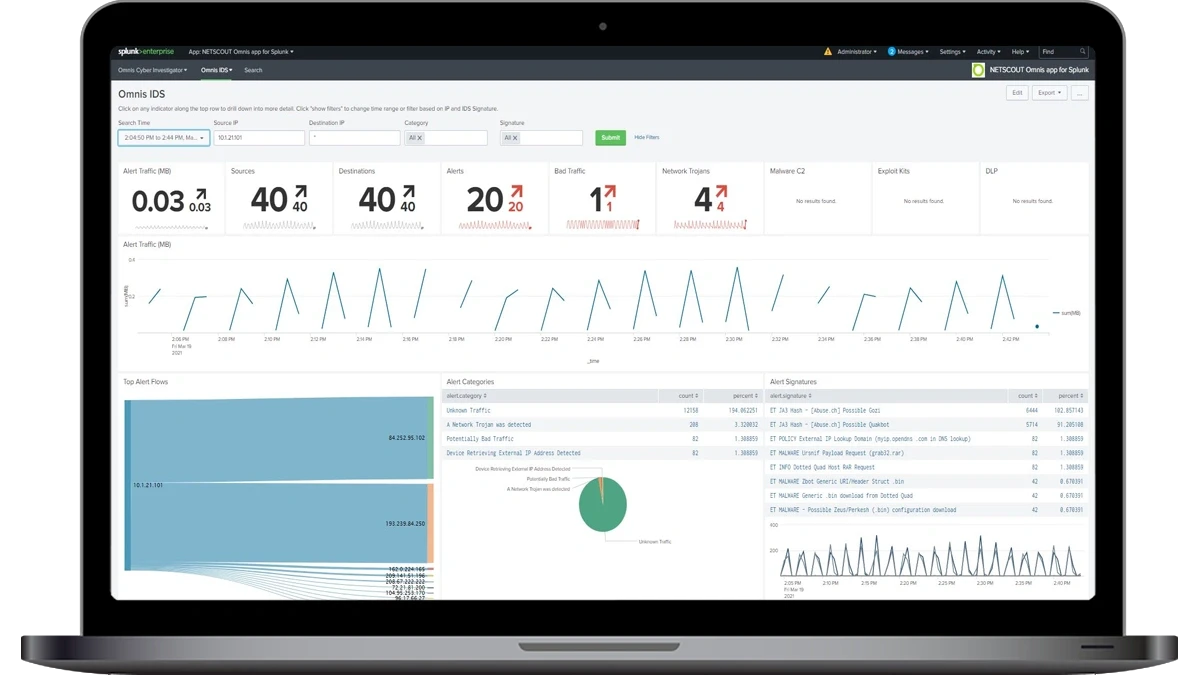
Omnis™ IDS uses open standards, APIs, and intuitive security workflows to easily integrate into existing security stacks and processes. It can be configured to forward security threat events and alarms to third-party SIEM systems, including Splunk, for consolidated security event management.
NETSCOUT Omnis App on Splunk illustrates the Omnis IDS solution's seamless integration capabilities, the result of leveraging open standards to operate with existing SIEMs, such as Splunk.
What is a network IDS?
An intrusion detection system (IDS; also intrusion protection system or IPS) is a device or software application that monitors a network or systems for malicious activity or policy violations. Any intrusion activity or violation is typically reported either to an administrator or collected centrally using a security information and event management (SIEM) system. A SIEM system combines outputs from multiple sources and uses alarm filtering techniques to distinguish malicious activity from false alarms.
One Smart Question
Resources
Related Pages
Faster, Smarter Incident Response Starts with the Right Data.
Omnis Network Security is a holistic cybersecurity platform for comprehensive network visibility, threat detection, investigation, and protection.

Contact NETSCOUT Today
To learn more about how NETSCOUT can help your company, speak to one of our highly experienced subject matter experts.

