Deterministically Accurate, Actionable Threat Intelligence at a Global Scale
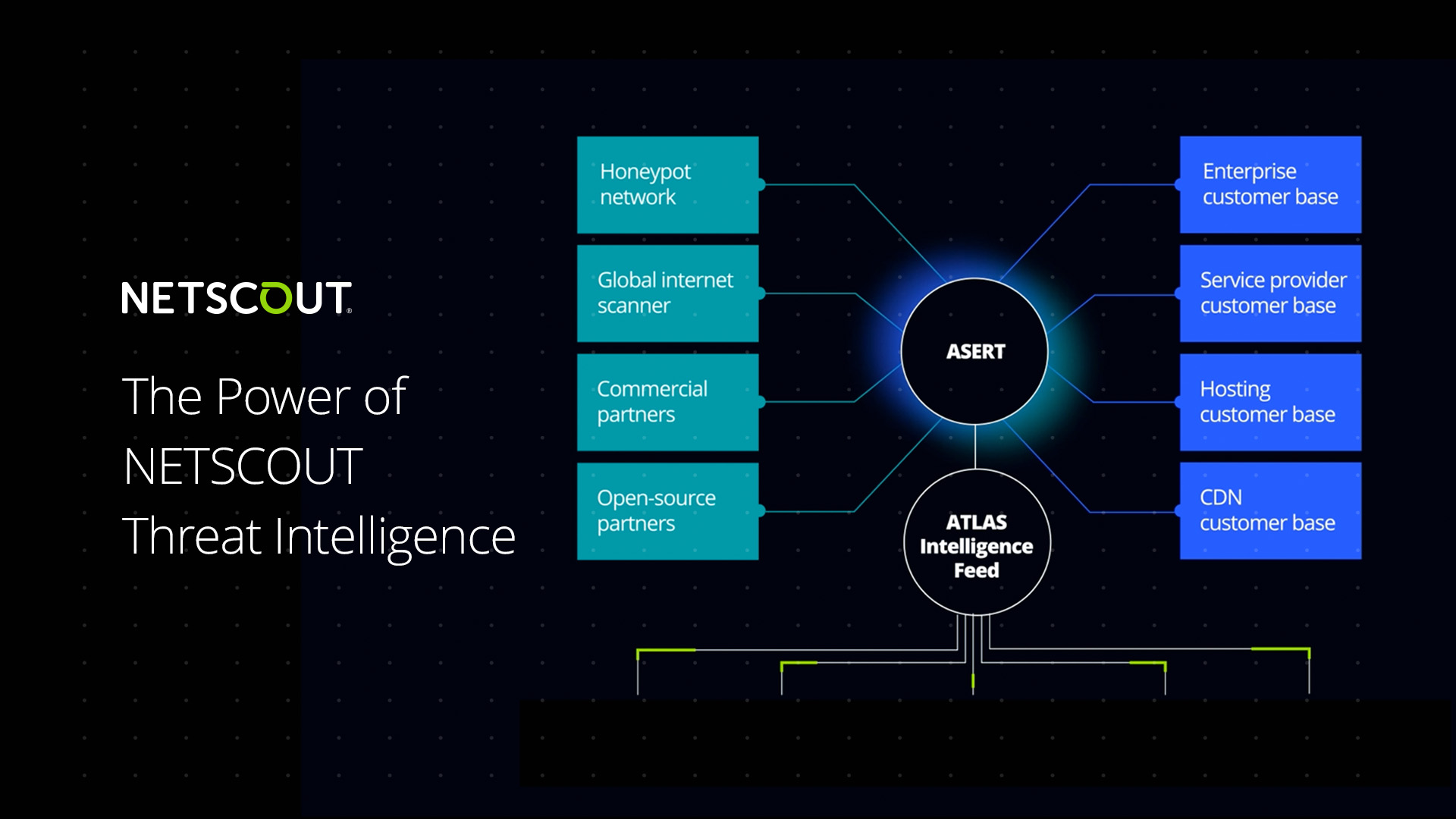
As cyber threats continue to increase in frequency and sophistication, mature security teams will not only rely upon the latest cybersecurity technology but also highly curated threat intelligence that arms these products. The NETSCOUT ATLAS global threat intelligence system monitors over 800+ Tbps of Internet traffic in real-time across more than 500+ ISPs and 3,000+ enterprise sites from over 125+ countries, representing two-thirds of the routable IP space and up to 50% of all internet traffic at any given moment.
This visibility, combined with our AI-powered analysis processes and the expertise of NETSCOUT’s ASERT Team, has enabled NETSCOUT to produce more deterministically accurate and actionable threat intelligence in real-time. This actionable intelligence is published via the ATLAS Intelligence Feed and automatically arms all NETSCOUT Arbor DDoS attack protection products with the latest DDoS attack tactics and methodologies, known sources of DDoS attacks, and Indicators of Compromise, so organizations can protect themselves from DDoS attacks and other cyber threats and automatically adapt protections as those attacks change vectors.
AI Powered Threat Intelligence
Automated Threat Intelligence Improves Adaptive DDoS Protection
Adaptive DDoS Protection or ADP is an added layer of protection that employs an automated artificial intelligence driven analysis process that detects evolving attacks that are not blocked by current countermeasures within Arbor Edge Defense (AED). It then creates recommendations within Arbor Enterprise Manager (AEM) for changes in countermeasures and configurations to block these newly detected attacks. These recommendations can also be set to automatically mitigate these new attacks. This repeating process is driven by the unmatched Threat Intelligence provided by the ATLAS Intelligence Feed.

DDoS: Automated DDoS Reputation Blocking
By identifying current active attackers from our unique worldwide ATLAS DDoS attack data, and identifying current active hosts that are part of DDoS botnets, AIF is designed to enable our products to detect and block inbound DDoS attacks quickly, automatically, and accurately, without the risk of false positives that can come from non-human curated automation operating in software alone.

DDoS: Automatically Prevent Blocking of Legitimate Services
Automatically assists in processes to avoid blocking search crawlers and other desirable web content that may trip DDoS countermeasures and be blocked during attack.
Improves accuracy of attack blocking while avoiding blocking legitimate traffic.
Provides significantly more intelligence from expanded analysis pipeline and intelligence sharing partnerships

Cyber Threats: Automated Blocking of Inbound Cyber Threats and Malicious Traffic
Artificial Intelligence-powered Threat Intelligence allows AIF to identify known active sources of Internet vulnerability scanning and brute force exploit attempts, as well as other bulk commodity threats. Our botnet intelligence feed uses our Honeypot network to understand when known botnet hosts are trying to infect other hosts on the network. This becomes actionable intelligence because we correlate the scan results with actual attack data from our worldwide collection to identify which botnet hosts are launching attacks in real time. This is designed to enable our products to automatically detect and block commodity threats before they enter the network, and decrease the load on other security devices that may be struggling to keep up during active attacks.

Cyber Threats: Automated Internal Threat Detection and Blocking
Using the breadth of our Artificial Intelligence-powered global attack intelligence, we will automatically detect, analyze and identify malware that may be involved in probing activities currently operating on your network and identify other advanced persistent threats. Malware IoCs enable NETSCOUT solutions to detect malware communication with a special focus on known botnet Command and Control infrastructure. NETSCOUT solutions detect infected hosts and threats resident inside the network, including APTs, and disrupts kill chains by blocking their outbound communication to prevent downloading additional malware payloads or communicating with command and control servers that are part of the kill chain.

Resources
Related Pages
Helping customers combat the ever-increasing frequency and complexity of DDoS attacks requires worldwide visibility, advanced threat analytics, continuous real-time cyber threat intelligence research, and recommended best practices.
Whether you are a service provider or have a complex enterprise network, Arbor Sightline helps monitor and identify networking and security issues at any network scale with AI and ML-powered insights.
Filter out malicious traffic while allowing legitimate traffic to pass through, at any scale, with Arbor Threat Mitigation System (TMS).

Contact NETSCOUT Today
Talk to a subject-matter expert to see how Omnis AI Insights supports your observability, security, and AI-driven initiatives.

