The New Network Has No Boundaries
Enterprises need new tools to truly see and understand their networks, so that data can be protected.

What happens when your network is no longer yours?
Behind the scenes, and behind the screens, at companies large and small, your network is increasingly something that exists outside of your control. The systems that power corporate work have fundamentally changed, as existing trends toward mobile workforces, cloud-based SaaS applications and device flexibility have been accelerated by the global pandemic. “When you move applications to the cloud, you’re emulating a network. And it’s not your network. It’s the cloud provider’s network. It’s a virtual network where things are changing all the time,” says Jon Oltsik, senior principal analyst and ESG fellow at Enterprise Strategy Group. “That didn’t happen on a traditional network.”
In the current (and future) environment, the old guardrails—the physical walls of the office or the digital barriers of VPNs and firewalls—offer far less protection. According to NETSCOUT, a leading provider of network management and security tools, malicious events that overloaded VPNs and firewalls increased 21% from 2019 to 2020, as attackers targeted the growing remote workforce. Meanwhile, as threat surfaces expand and bad actors grow more sophisticated in their attacks, security increasingly depends on the ability to see inside these more complex, cloud-based networks. “It’s important that you have visibility on everything, especially as attacks generally start off looking like regular traffic or behavior from a user,” Oltsik says. “And then they slowly look at the network, get different credentials and do tremendous damage. You want to catch them early.”
Meaningful Visibility
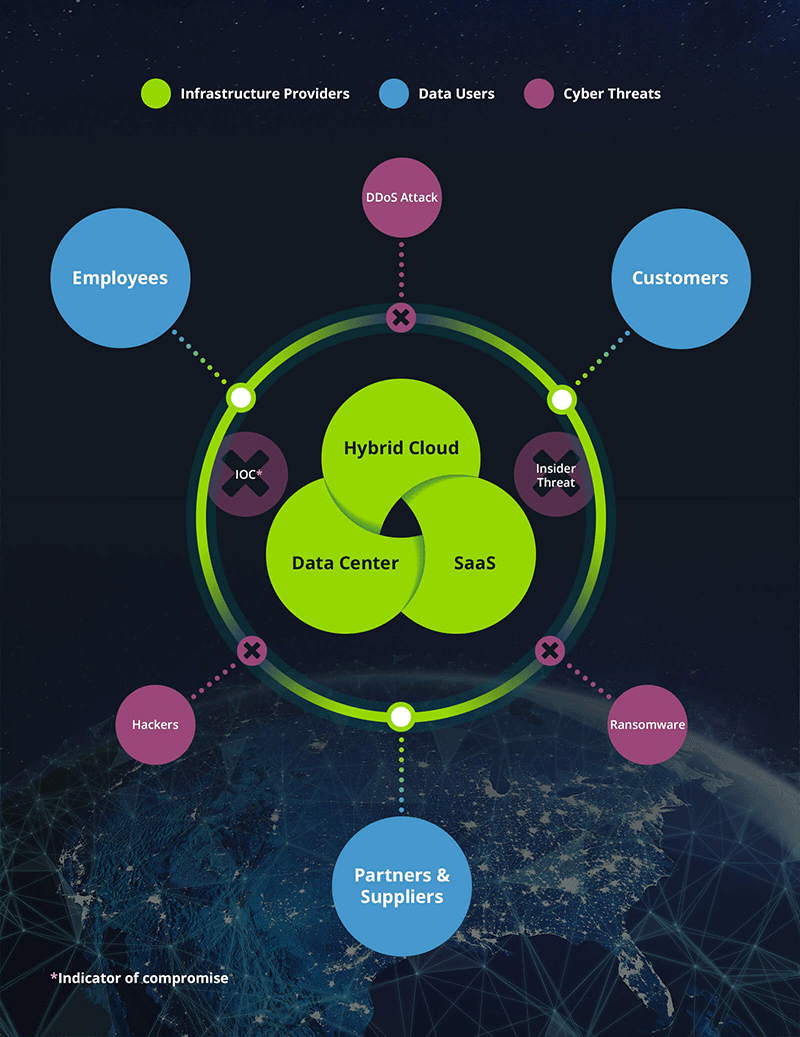
Meaningful visibility is not simply a matter of seeing who is accessing the network and how. It’s an understanding of the interconnectedness of an enterprise’s complete digital infrastructure. It’s also an understanding of how different that looks today, compared to just a few years ago, when cloud solutions weren’t as dominant and remote work was less common. People inside the business don’t always understand the reach of their networks, what they have deployed, where they’re exposed or what their dependencies are, says Hardik Modi, area vice president of engineering, threat and mitigation products at NETSCOUT.
“There’s any number of instances, for example, where the adversary knows to look for endpoint protection and turn it off, or find access through endpoints that might be less well protected, whether routers or IoT devices,” he says. According to NETSCOUT’s latest Threat Intelligence Report, an attacker can scan and compromise a new IoT device in five minutes or less.
Tools like NETSCOUT’s Smart Edge Protection technologies are designed to shine light on those risks by viewing data across physical, virtual and public cloud environments, analyzing traffic and using automation to identify risks and threats to the network. By focusing on the network itself, Modi says smart data tools can detect potential problems that endpoint security technologies on their own might miss. “Because we have the full fidelity, you can drill down and then you can zoom back out,” he says. “That allows us to give you really pervasive visibility.”
Data, Forward
In the face of expanding threat landscapes and emboldened attackers, enterprises must be constantly vigilant. How fast security software can act is critical. “Companies need to be proactive to mitigate known vulnerabilities and actively monitor all networks and systems to find intrusions as rapidly as possible,” says Curtis Franklin, senior analyst in cybersecurity at Omdia. “Dwell times—the length of time an intrusion is in a system before detection—remain very long, stretching for months and even years. Finding and remediating any suspicious activity is key to limiting the damage threat actors can do.”
Because we have the full fidelity, you can drill down and then you can zoom back out. That allows us to give you really pervasive visibility.Hardik Modi, Area Vice President of Engineering, Threat and Mitigation Products, NETSCOUT
And in today’s environment, Franklin says the good guys and the bad guys are using similar tools, like machine learning and artificial intelligence, which allow both sides to operate faster, without a need for consistent human intervention. “Threat actors use them to increase the effectiveness and lower the costs of their attacks, while defenders use them to separate noise from actual danger signals, responding to attacks more quickly than human analysts could,” he says. “Defenders, for example, use AI to defend against rapidly evolving threats that have not yet generated recognizable signatures, and attackers are using it to launch phishing attacks involving the same type of bot technology legitimate companies use to deliver customer service.”
Data can itself be a weapon against data, when used effectively. Better data results in better learning for the algorithms it trains, Modi says—and the ability to stay a step ahead in defending the networks of today. “If you can take trained, curated metadata, well-formatted and understood, and train your algorithms on that, you’re looking at a different set of outcomes,” he says. “The nature of data we’re extracting allows for better, enhanced outcomes using machine learning and data science.”
Tools like NETSCOUT’s Adaptive Service Intelligence, Modi says, are able to provide real-time insights and analytics from traffic data across all networks, whether on premises or in the cloud. And in the modern threat environment, enterprises can’t fall even a half-step behind. “There are motivated human adversaries, constantly looking for ways to negatively impact you using networks. They are where they are, you are where you are, and there’s a network that connects you,” Modi says. “That visibility has to enable the discovery of these systems, your core systems, and the relationships and dependencies between them. That is core to defending against intrusion.”
- - -
This article was written and produced in partnership with the Wall Street Journal. Wall Street Journal Custom Content is a unit of The Wall Street Journal Advertising Department. The Wall Street Journal news organization was not involved in the creation of this content.