Distributed denial-of-service (DDoS) attacks are a major risk for enterprise virtual private network (VPN) concentrators. Protecting these servers is paramount for business operations and continuity. Without a secure VPN, remote workers lose access to enterprise network resources, applications, and data, impacting productivity and work output.
An enterprise VPN is used differently from a consumer VPN. An enterprise VPN is deployed primarily to enable secure authenticated access to corporate resources via an encrypted tunnel to transmit potentially sensitive information between a remote employee and the enterprise network. A consumer VPN, however, is typically used to hide one’s source IP addresses for various reasons, including privacy.
DDoS attacks are rampant against major enterprises and service providers, with more than 7 million DDoS attacks in the second half of 2023 alone. The threat is real, and businesses must work diligently to protect all areas of their networks.
Identifying Vulnerabilities in Your Enterprise VPN
Enterprise VPNs can be vulnerable to a multitude of vulnerabilities. For example, weak credentials or reused passwords for logging into the VPN can be exploited, giving bad actors easy access to the environment. An enterprise VPN’s configuration can also determine its cyber resilience. Granting the VPN too much access to the network instead of only to the areas it needs to access can lead to broader damage should a breach occur.
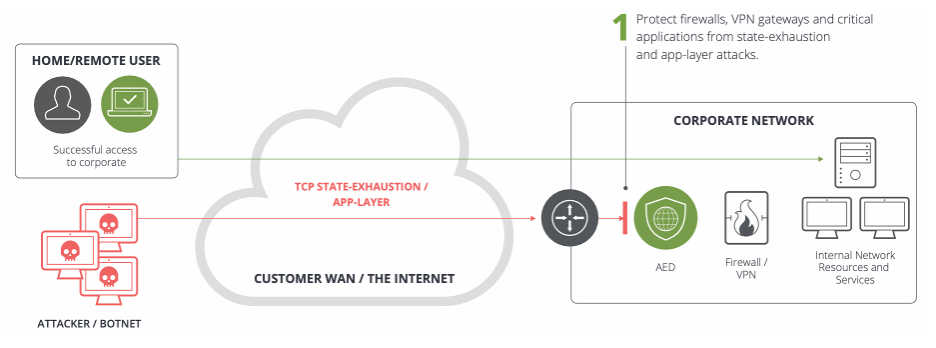
An in-depth audit can help determine these and other vulnerabilities. By determining the overall position of your VPN’s security, you can deploy additional measures to shore up security and prevent breaches. In addition, mitigating and protecting against volumetric and state-exhaustion DDoS attacks aimed at the VPN itself or at firewalls can further strengthen cybersecurity and maintain availability and connectivity.
Proactive Measures to Secure VPNs Against DDoS Attacks
Implementing a robust firewall can help protect a VPN from several types of cyberattacks, but VPNs struggle against DDoS attacks. Having a stateless DDoS protection solution can protect stateful devices from being overwhelmed by state-exhaustion attacks.
Like a firewall, instruction detection systems (IDSs) and intrusion prevention systems (IPSs) can help identify and prevent cyberthreats from attacking VPNs. However, DDoS attacks easily overwhelm these systems, allowing them to disrupt the VPN’s availability and harm productivity and connectivity.
The best way to maintain your VPN’s availability is with a dedicated, customized DDoS protection solution that protects on-premises, in the cloud, and everywhere in between. The right solution can detect, mitigate, and combat DDoS attacks of all shapes and sizes, maximizing uptime and minimizing revenue loss due to a lack of productivity.
Strategies for VPN DDoS Protection
Utilizing a customized and comprehensive approach to DDoS protection is key to maintaining the availability of important VPN services. NETSCOUT’s hybrid on-premises and in-cloud approach shines in this area, allowing for a robust stance against DDoS attacks of all shapes and sizes.
By meeting attackers where they are in the network environment, whether that be on-premises or in the cloud, enterprises can detect, combat, and mitigate DDoS attacks faster than ever. This is done by deploying DDoS protection solutions throughout the network architecture, not just in one place, to ensure that threats are met head-on with stout defenses. In addition to DDoS protection solutions, common security practices such as multifactor authentication can prevent attacks from succeeding and maintain the availability of important enterprise networks.
Learn more about NETSCOUT’s adaptive DDoS protection solutions.
