- APT
- DDoS
- IOT
NETSCOUT Threat Intelligence Report
1H 2019 Reveals New Findings on IoT Vulnerabilities, CyberCrime Innovation, Nation-State Actors, and Rising DDoS Attacks

"It’s hard to express the scale of today’s cyber threat landscape, let alone its global impact." - Hardik Modi, Senior Director of Threat Intelligence
Executive Summary
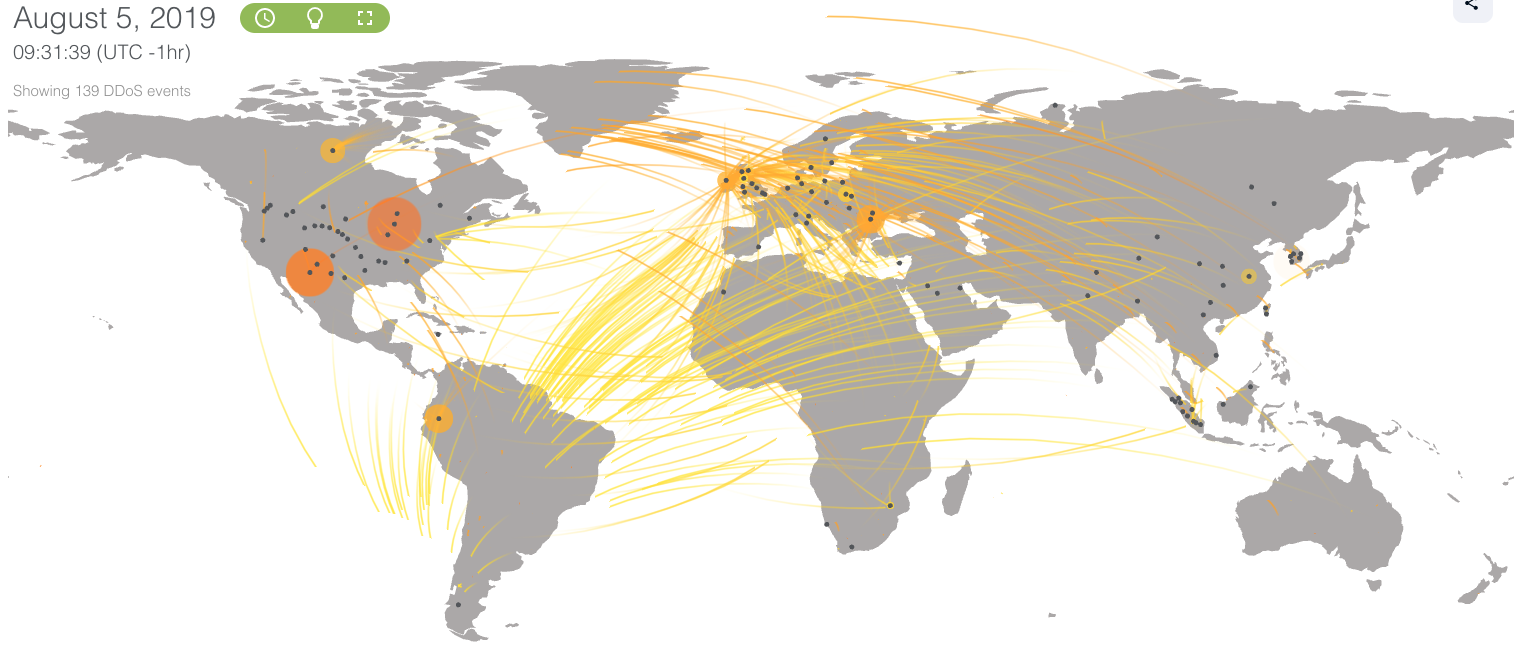
In the past six months, there were nearly four million DDoS attacks around the world and that attack frequency grew by 39 percent in the first half of 2019. The NETSCOUT ASERT team, in conjunction with our partner ReversingLabs, saw 20,000 unique samples per month from just one family of IoT malware. We also discovered it can take only five days from the discovery of a new attack vector to the availability of tools for the script-kiddie designed to exploit that vulnerability.
But those numbers, while startling, don’t fully convey the impact of that steady drumbeat of new threats. As our latest Threat Intelligence Report shows, cybercrime has entered the mainstream of our culture to an unprecedented extent, and it is here to stay. We already saw online gamers hire DDoS botnets to take down opponents; now, college students can easily do the same—to take down testing platforms. Globally, cyber tactics like malware, DDoS attacks, and social engineering are increasingly used by geopolitical adversaries. Ransomware has become common enough to prompt 225 US mayors to sign a resolution vowing not to pay ransoms to hackers.
Key Findings
IoT devices are under attack within minutes. It can take only five days from new attack vector discovery to weaponization, giving attackers fast access to inexpensive and devastating tools for revenge.
Rapid weaponization of vulnerable services continued, as attackers took advantage of everything from smart home sensors to smart phones, routers, and even Apple software; We have also seen proof-of-concept malware targeting IoT devices behind firewalls, which increases the risk of attack and adds another layer of complexity to a defender’s responsibility.
Even college students can hire botnets to take down testing platforms. The NETSCOUT Security Operations Center helped one university successfully thwart targeted local attacks to online test platforms and curriculum.
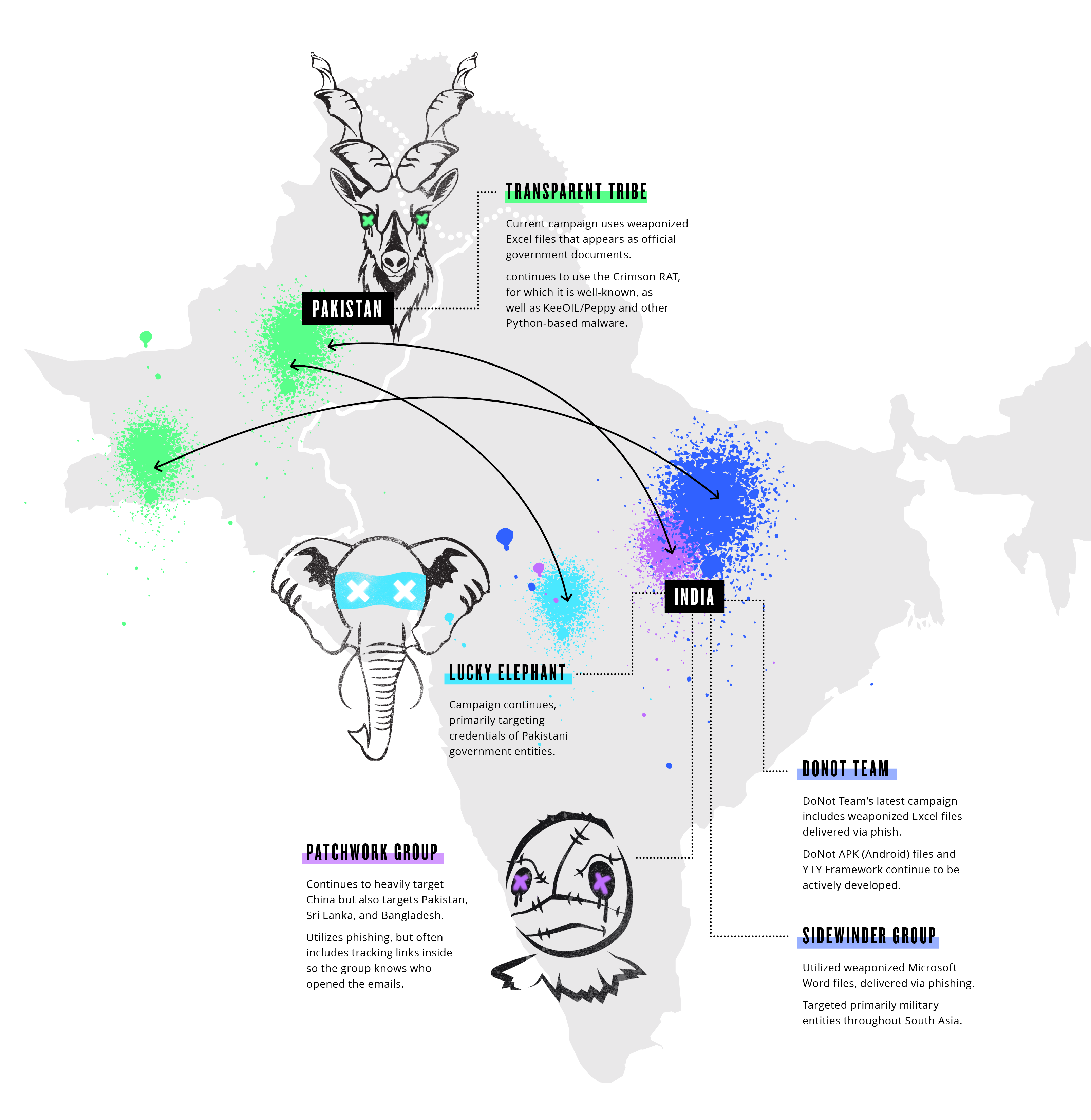
Geopolitical skirmishes increasingly employ cyber tactics ranging from malware and DDoS attacks to social engineering and misinformation as part of their toolkit. India and Pakistan exemplify the increasing use of cyber tactics as they targeted each other with a series of campaigns in the first half of 2019.
While bespoke and sophisticated malware continues to make the rounds, many campaigns had little to no malware at all and relied entirely on deception and social engineering, since email remains the dominant intrusion vector.
Learn More
As threats grow across the landscape, NETSCOUT's unique position protecting enterprise networks and the internet through our service provider customers gives us wide visibility into this dynamic and ever-changing environment. NETSCOUT’s Arbor Active Threat Level Analysis System (ATLAS®) has actively monitored the global internet threat landscape since 2007. Today, it provides us with visibility into approximately one-third of the global internet.
By drawing on that comprehensive view with analysis driven by NETSCOUT's ATLAS Security Engineering & Response Team (ASERT), we have created a representative view of the threat landscape as we observed in the second half of 2018 based on all our data and driven by extensive research and analysis.
Download the full report
You can also register for a webinar on the report results. Register Here.
Cyber Threat Horizon Launch
In conjunction with this report, we’re also launching an information service designed to represent the threat landscape in real time. NETSCOUT Cyber Threat Horizon (https://horizon.netscout.com) is powered by ATLAS and represents much of the same underlying data you’ll see this in report. Our objective is to enhance situational awareness for key stakeholders – those who care about how attack activity impacts organizations like themselves worldwide. As you read this report and reflect on our observations from the past six months, please turn to Cyber Threat Horizon to see what is happening today.
- Advanced Persistent Threats
- Attacks and DDoS Attacks