What is a Reflection Amplification Attack?
Let’s start by defining reflection and amplification attacks individually.
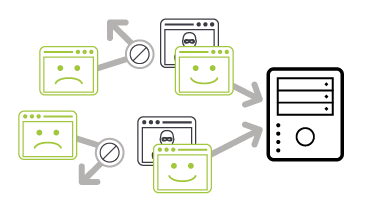
A reflection attack involves an attacker spoofing a target's IP address and sending a request for information, primarily using the User Datagram Protocol (UDP) or in some caes, the Transmission Control Protocol (TCP). The server then responds to the request, sending an answer to the target’s IP address. This "reflection" - using the same protocol in both directions - is why this is called a reflection attack. Any server operating UDP or TCP-based services can be targeted as a reflector. Adequate DNS DDoS protection solutions can assist in mitigating these types of attacks.
Amplification attacks generate a high volume of packets that are used to overwhelm the target website without alerting the intermediary. This occurs when a vulnerable service responds with a large reply when the attacker sends his request, often called the “trigger packet”. Using readily available tools, the attacker is able to send many thousands of these requests to vulnerable services, thereby causing responses that are considerably larger than the original request and significantly amplifying the size and bandwidth issued to the target.
A reflection amplification attack is a technique that allows attackers to both magnify the amount of malicious traffic they can generate and obscure the sources of the attack traffic. This type of distributed denial-of-service (DDoS) attack overwhelms the target, causing disruption or outage of systems and services.
The most prevalent forms of these attacks rely on millions of exposed DNS, NTP, SNMP, SSDP, and other UDP/TCP-based services.

What Are the Signs of a Reflection Amplification Attack?
Reflection amplification attacks are relatively easy to identify because they usually involve a large volumetric attack. Such attacks are indicated by a substantial flood of packets with the same source port to a single target. It is important to note that incoming packets rarely share the same destination port number, which is why this is a good indication of an attack. Attackers will often use multiple vulnerable services at the same time, combining these into extremely large attacks.
Defend Against Reflection Amplification Attacks with NETSCOUT

Why Are Reflection Amplification Attacks Dangerous?
Reflection amplification attacks are dangerous because the servers used for these types of attacks can be ordinary servers with no clear sign of having been compromised, making it difficult to prevent them. Attackers are attracted to reflection amplification attacks because they don’t require sophisticated tools to launch. These attacks require minimal effort to create enormous volumetric attacks by using a modest source of bots or a single robust server.
How Can Organizations Mitigate and Prevent Reflection Amplification Attacks?
The primary defense against reflection amplification attacks is to block the spoofed source packets. Because attacks come from legitimate sources, using trusted services such as DNS and NTP, it becomes difficult tell the difference between genuine user workloads and reflected traffic generated by attackers. Adding to the challenge, when a service comes under attack, legitimate user traffic may be forced to retry responses due to the slowdown in service, possibly causing these retries to be falsely identified as DDoS attacks in their own rite.
Organizations can take the following steps to mitigate reflection amplification attacks:
- One general DDoS mitigation strategy is to employ rate limiting, which can be applied to destinations or to sources, to prevent systems from being overwhelmed. Destination rate limiting may inadvertently impact legitimate traffic, making this a less desirable approach. Rate limiting the source is considered more effective. This approach restricts sources based on a deviation from a previously established access policy.
- Blocking ports that are not needed can reduce vulnerability to attacks. This does not prevent attacks on ports that are used by both legitimate and attacker traffic, however.
- Traffic signature filters can be used to identify repetitive structures that are indicative of an attack. The downside to such filtering may be its impact on performance. Inspecting every packet may ultimately overwhelm defenses.
- Threat intelligence services can help organizations identity vulnerable servers, allowing them to block the IP addresses of these vulnerable servers. This proactive approach can provide more precise mitigation. Netscout/Arbor publishes a set of AIF filter lists on a regular basis which contain up-to-date information on vulnerable servers which are actively being used as DDoS Reflectors.
NETSCOUT Protects Against Reflection Amplification Attacks
How can NETSCOUT help?
NETSCOUT's Arbor DDoS solution has been protecting the world's largest and most demanding networks from DDoS attacks for more than a decade. We strongly believe that the best way to protect your resources from modern DDoS attacks is through a multi-layer deployment of purpose-built DDoS mitigation solutions.
Only with a tightly integrated, multi-layer defense can you adequately protect your organization from the full spectrum of DDoS attacks.
Arbor SP/Threat Mitigation System
NETSCOUT customers enjoy a considerable competitive advantage by getting both a micro view of their own network, via our products, combined with a macro view of global Internet traffic, via NETSCOUT Cyber Threat Horizon, an interface to our ATLAS threat intelligence and a DDoS Attack Map visualization.
