Stop DDoS Attacks with Automated Artificial-Intelligence Backed Technology and Unparalleled Global Threat Intelligence
DDoS attacks continue to be the easiest and least expensive method for bad actors to cripple your organization by negatively impacting your network’s availability to users and customers. Whats new is complex multi-vector attacks and probing activity that manifest as nuisance outages or mysterious application downtime and are designed to evade existing defenses including upstream protections. To address these DDoS threats, security teams need solutions that can identify and mitigate attacks of any size and duration automatically without impacting legitimate traffic and organization productivity.
NETSCOUT Arbor Edge Defense® (AED) is uniquely positioned on the network edge (i.e., between the internet router and the firewall) to provide inline, always-on, DDoS protection. To leverage this unique and valuable position, AED uses Artificial Intelligence driven packet analysis, decades of DDoS protection and mitigation expertise to stop all DDoS attacks automatically.
Resiliency Without Compromise
Cyber Defense Magazine’s Global InfoSec Awards
NETSCOUT’s Arbor Edge Defense and ATLAS Intelligence Feed Named Market Makers for Threat Intelligence

What's New in Arbor Edge Defense
Learn the latest features and functionalities in Arbor Edge Defense and Arbor Enterprise Manager. Enhance DDoS protection with the latest features that leverage advanced AI/ML technology.

Artificial Intelligence Powered Adaptive DDoS Protection
Adaptive DDoS Protection for Arbor Edge Defense (AED) is NETSCOUT's AI innovation that automates the fine-tuning of DDoS attack mitigation, without the risk of over-blocking legitimate traffic.

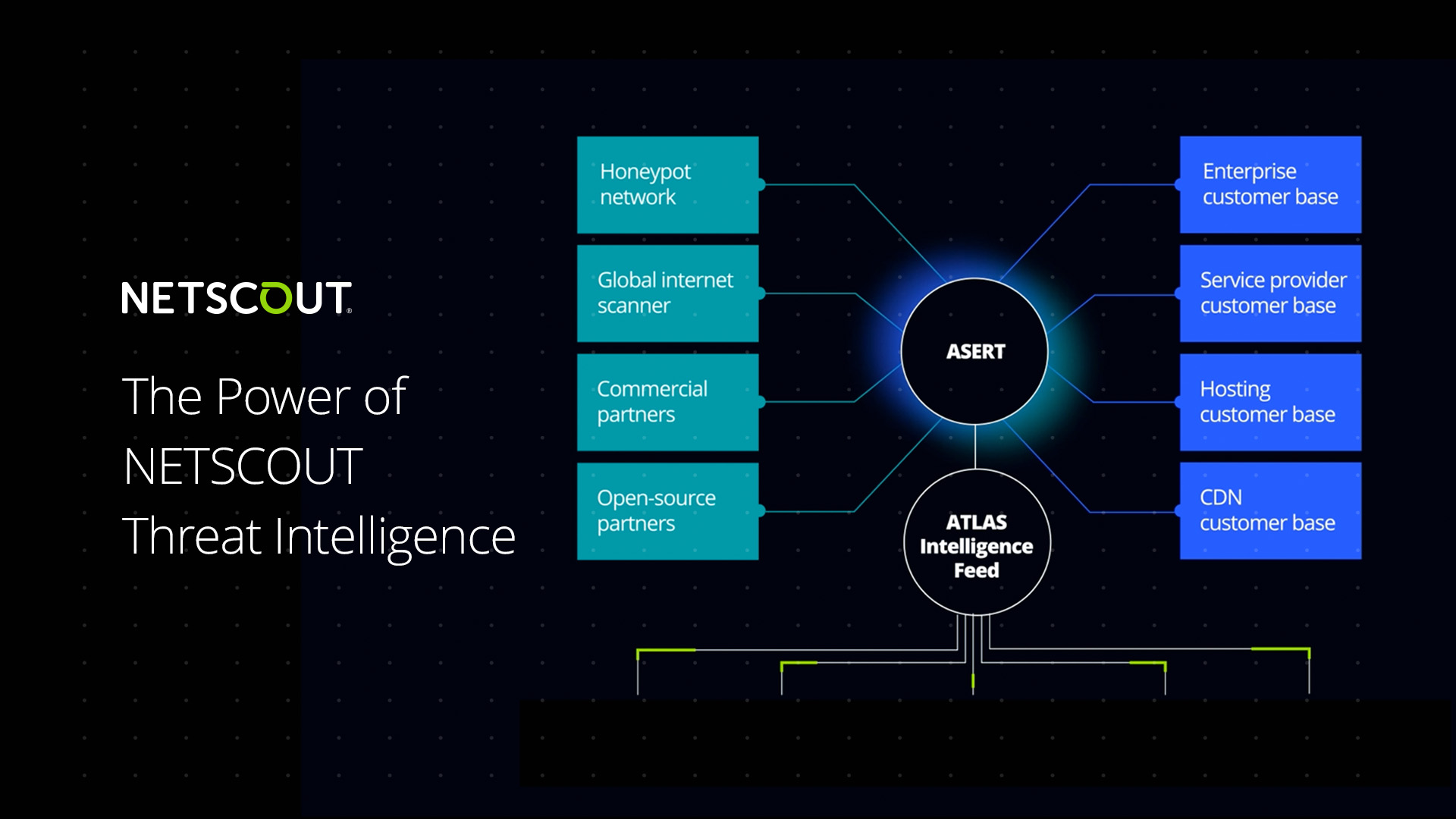
Unmatched, Artificial Intelligence Backed Threat Intelligence
Defending your network efficiently requires as much knowledge about your adversary as possible and the ability to operationalize that knowledge to automatically adapt defenses to the ever-changing attackers' tactics and techniques. NETSCOUT's advantage is our superior ATLAS global DDoS attack visibility system, which uses AI to automatically update the ATLAS Intelligence Feed which arms AED with the latest DDoS attack protection intelligence.
Why Arbor Edge Defense?
"Best class inline DDoS mitigation solution"
"Robust Solution for Mitigation of Attacks"
"Very reliable information"
"As an analyst, AED has helped me triage many alerts throughout the years."
Stateless, Always-On, AI Powered Perimeter DDoS Attack Protection
AED’s stateless, always-on DDoS attack protection at the perimeter of the network automatically stops inbound application-layer and state exhaustion DDoS attacks that can impact your most critical applications and firewalls.

Intelligently Integrated Hybrid DDoS Protection
AED’s cloud-signaling feature automatically and intelligently integrates on-premises mitigation with Arbor Cloud cloud-based mitigation to stop sophisticated, multi-vector DDoS attacks including volumetric attacks that overwhelm your internet circuit.

Non-DDoS Attack Protection
AED stops more than DDoS attacks. AED can automatically stop inbound scanning, brute force attacks, known malicious communication and malware (e.g., ransomware) using millions of IoCs from NETSCOUT’s world class ATLAS Intelligence Feed or third-party threat intelligence feeds.

Artificial Intelligence Powered Threat Intelligence
NETSCOUT’s AI threat curation capabilities are built on a foundation of unmatched global visibility into internet traffic and DDoS threats.

Artificial Intelligence Powered Adaptive DDoS protection
NETSCOUT’s Adaptive DDoS Protection solution for AED integrates AI-driven traffic analysis to detect new attacks, classify their nature, recommend tailored countermeasures and automatically mitigate the new attacks if required.

Resources
Related pages
Arbor Cloud provides industry-leading scrubbing capacity to enable powerful cloud-based DDoS protection to keep your applications up and running.
Arbor DDoS Protection delivers unmatched defense against the latest dynamic DDoS attacks. Backed by decades of experience, NETSCOUT's Arbor solutions secure the most complex networks.
ATLAS Intelligence Feed (AIF) provides up-to-date threat intelligence on the latest DDoS threats to our DDoS protection products. Automate defenses against trending attacks with AIF.
Helping customers combat the ever-increasing frequency and complexity of DDoS attacks requires worldwide visibility, advanced threat analytics, continuous real-time cyber threat intelligence research, and recommended best practices for mitigation from industry experts.
Faster, Smarter Incident Response Starts with the Right Data.
Find out everything you should know about DDoS (Distributed Denial of Service) attacks and learn how to protect your network with these tips from NETSCOUT.

Contact NETSCOUT Today
To learn more about how NETSCOUT can help your company, speak to one of our highly experienced subject matter experts.

