Was Memcached a Turning Point?
DDoS attacks remain a primary concern, but network and security hygiene is improving around the world.

Distributed-denial-of-service (DDoS) attacks are the primary concern for 2019, according to a survey of service providers conducted in the fall of 2018 and released in NETSCOUT’s 14th annual Worldwide Infrastructure Security Report. Among respondents, 88 percent cited DDoS attacks as their top concern, and the continued use of reflection/amplification techniques and ongoing exploitation of vulnerable Internet of Things (IoT) devices have many worried about an increase in high-volume attacks.
At the mid-point of the year, it turns out those service providers were right to be worried. According to the most recent NETSCOUT Threat Intelligence Report, attack frequency jumped 39% in the first half of 2019 compared with 1H 2018. The number of attacks between 100 Gbps and 400 Gbps dramatically increased, resulting in a staggering growth rate of 776%. The use of reflection amplification continues, as does the exploitation of vulnerable Internet of Things (IoT) devices. In fact, NETSCOUT’s honeypot research has shown that a new, unsecured IoT device connected to the internet will be scanned by attackers within five minutes. Some may recall that’s even faster than Microsoft Windows XP computers were compromised.
DDoS attackers tend to repeatedly exploit the same protocols and services, such as DNS and NTP, to maximize the scale of their attacks. This has continued, because the same poorly configured or unprotected protocols remain open and available to them year after year. The cycle of emerging stars (exploited protocols) has a rhythm: A new vulnerability is identified, and the attacker gets to work developing a tool to exploit it and to sell on the underground. Word gets out, and others start to reverse-engineer the tool and create their own tools to leverage the new exploit. Suddenly, this exploit is for sale on booter/stresser services to anyone with an internet connection and bad intentions. The time from the discovery of a new vulnerability to full-scale weaponization of the attack can be very short: in the case of Memcached, it took five days before the attack code was available on GitHub.
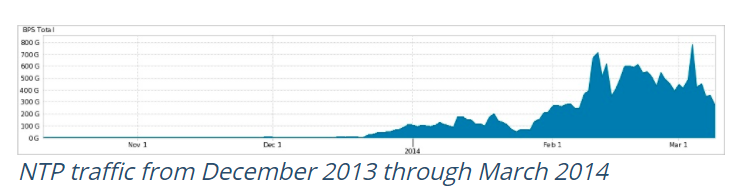
In 2013, malware exploiting NTP was weaponized, and it emerged overnight as a star in the world of DDoS attacks. Attack tools and booter/stresser attack services using the NTP protocol quickly became widely available, driving high-volume NTP reflection/amplification DDoS attacks to the top of the charts. At the time, NTP replaced DNS as the prominent reflection/amplification vector. Out with the old, in with the new.
Memcached attacks are a great example, and perhaps a turning point. Open source and free, Memcached is a high-performance, distributed memory caching system designed to optimize dynamic web applications. Early in 2018, NETSCOUT and others saw a significant increase in the abuse of misconfigured Memcached servers residing on internet data center networks and using them as unsuspecting tools in DDoS reflection attacks. At that time, there were approximately 50,000 unsecured Memcached installations on the internet that could be used in DDoS attacks.
The amplification capabilities of Memcached servers is so great that if you send a single request, that request could send back 500,000 responses. This led to the terabit attack era. In February 2018, Akamai reported a 1.3 Tbps attack targeting Github, and a week later NETSCOUT disclosed that it had helped a North American service provider customer successfully mitigate a 1.7 Tbps attack. In both instances, these were Memcached attacks.
New Focus on Security
After Memcached, two things happened. One is that the network and security community became more focused on securing infrastructure, especially anything that is open to the internet. NETSCOUT has been talking about this for years, warning time and again that these unsecured protocols and services would be abused by attackers. Increased awareness post-Memcached has helped spur some positive action. Perhaps it was the shock of a terabit attack, and the potential implications, that caused a change in behavior after years of ignoring these same pleas? In the weeks following the February attacks, the number of unsecured Memcached servers dropped very quickly—down from 50,000 to 20,000 and then gradually declining to only 3,500 installations by June 2018. People finally got the message.
More recently, we have seen DDoS attacks using the Constrained Application Protocol (CoAP) in China. Some are calling them the next big thing for DDoS attacks. CoAP is a lightweight protocol that is very similar to Memcached in the way it caches information. When NETSCOUT first saw these attacks, we looked at how many vulnerable devices were out there and saw about 500,000, but that number very quickly was reduced in volume. A similar thing happened with wireless devices from Ubiquity/Unify that had a vulnerability being used for reflection attacks. The number of exploitable devices was reduced from 300,000 to 150,000 in a few weeks. Even IoT is getting a little bit better. Some newer devices are starting to have software updates and are better secured by default, and network administrators are increasingly trying to block them from the internet.
It seems so basic and easy to do, especially when you consider the stakes. With massive amplification capabilities, attackers have taken us into the terabit attack era, and we have nobody to blame but ourselves. We’ve made their job easier, we’ve made them more powerful, and we allow them to exploit the same protocols and services year after year. After the shock of Memcached, we’re seeing better network and security hygiene around the world. Let’s hope that continues. It’s the least we can do.
Download NETSCOUT’s 14th annual Worldwide Infrastructure Security Report
Steinthor Bjarnason is a principal security engineer with ASERT.