Single-Layer Defense Is at Best a Deterrent to DDoS Attacks
A multilayer hybrid defense strategy has become a requirement for protecting your network.

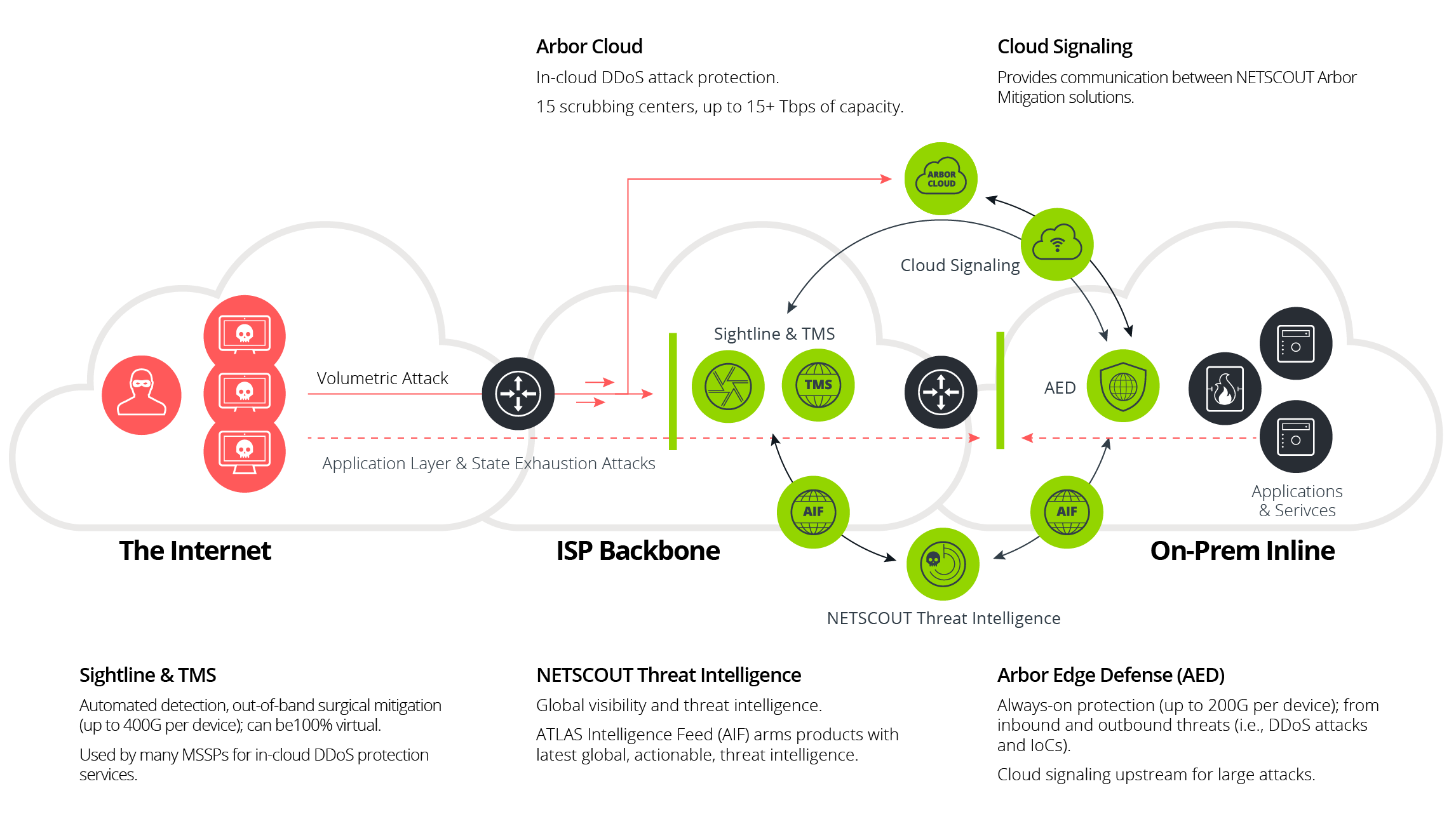
Industry analysts are coming to grips with the fact that due to today’s growing frequency (e.g., 6.4 million attacks in 2H 2023), size (1.1Tbps), and complexity of distributed denial-of-service (DDoS) attacks, a multilayer hybrid defense strategy has become a requirement. Furthermore, due to the creation of new attack vectors (threat actors exploited or weaponized seven new reflection/amplification DDoS attack vectors within the last seven months); the number of attack vectors being used in a single attack (31 attack vectors deployed in a single attack); and what’s known as a dynamic DDoS attack, which changes vectors based on the defense that is presented, on-premises protection, with its inherent attack management agility and efficiency, is a priority. It should be considered the foundation of a comprehensive adaptive DDoS protection that partners with network infrastructure and cloud-based mitigation services.
DDoS Protection Challenge
As DDoS attacks continually become larger and more prevalent, cloud-based DDoS mitigation services have become popular choices for customers who need protection that can react quickly and scale effectively. These services commonly come from content delivery network (CDN) providers, internet service providers (ISPs), or ISP-agnostic DDoS protection services providers. Whether it’s always-on or on-demand, cloud-based DDoS scrubbing services are a useful and necessary way of protecting your organization. To augment these cloud solutions, it is essential to add on-premises mitigation capacity to effectively combat all DDoS attacks.
Most DDoS attacks combine volume, application-layer, and state-exhaustion techniques to bring down their targets. Although cloud-mitigation solutions typically are used for stopping high-volume and some state-exhaustion attacks, some state-exhaustion and most application-layer DDoS attacks can go completely undetected when the volume is low or the attack patterns are not identified and stopped by the cloud-based mitigation tools responsible for blocking high-volume attacks. Beyond DDoS, any attacks actively targeting services, malicious traffic from a potentially compromised host, or other indicators of compromise (IoCs), still need to be not only detected but stopped. On-premises mitigation is a necessary addition to cloud mitigation for the protection of business-critical services.
Single-Layer DDoS Mitigation Risk
Dangerous smaller attack traffic is still reaching your business-critical services and networks. That traffic could be state-exhaustion attacks, application-layer attacks, or something even more dangerous such as attempts to compromise hosts in order to increase the payloads and capacity of malicious botnets. Since cloud mitigation does little to stop lower-volume attacks and isn’t designed to detect or mitigate traffic based on IoCs and threats, your network and services are still vulnerable to compromise and downtime.
DDoS Attack Mitigation Details
DDoS attack mitigation techniques typically are divided into three major categories:
- Cloud-based managed DDoS protection services offered by an organization’s CDN, ISP, or carrier-agnostic cloud-based mitigation services such as NETSCOUT Arbor Cloud
- Network infrastructure, such as routers with techniques such as access control lists, source-based Border Gateway Protocol (BGP) Remote Triggered Blackholing (S/RTBH), or BGP Flowspec
- Specialized intelligent DDoS mitigation system (IDMS) devices such as NETSCOUT Arbor Edge Defense (AED)
Increasingly, enterprise network and security teams are looking to combine these three approaches for more scalable and effective DDoS defense. Network infrastructure can be used to block DDoS attack vectors that involve high volumes of traffic matching a static network layer signature, such as a well-known port, protocol, and packet size. This leaves other attack components, such as orphaned IP fragments, other protocol traffic, state-exhaustion attacks, or application-layer attacks requiring additional analysis or authentication to be blocked by the intelligent DDoS mitigation system (AED). In circumstances where ingress capacity itself is overrun by sheer volume, cloud-based mitigation is required.
NETSCOUT’s Solution
NETSCOUT Arbor Cloud signaling is one of the first solutions for automated and intelligent communication between on-premises DDoS protection devices (e.g., AED) and NETSCOUT Arbor cloud-based services, pioneering the multilayer defense approach. Arbor Cloud is an ISP-agnostic service that integrates with NETSCOUT’s Arbor DDoS protection ecosystem.
NETSCOUT’s multilayer protection strategy is designed to enable comprehensive DDoS protection in an increasingly complex environment. On-premises, dedicated DDoS mitigation devices such as AED provide stateless real-time protection and packet-level visibility that can be surgically tuned to any environment and can automatically and intelligently communicate with NETSCOUT Arbor Cloud or an ISP’s cloud-based DDoS protection service to provide optimal protection.
AED provides advanced packet-based protection against internet-scale threats, neutralizing the malware families that make up the global botnet threat. Armed with millions of reputation-based
IoCs, NETSCOUT’s packet-processing engine can detect and block inbound threats and outbound communication from internal compromised hosts that have been missed by other devices in the security stack—helping to stop the further proliferation of malware and other tactics used within crimeware and advanced-threat campaigns.
In Summary
Because of the damage that can be done by small-volume, short-duration attacks on an organization’s critical business applications and services as well as the requirement for near real-time mitigation to stop these attacks, an always-on packet-level mitigation solution that sits on the edge of your network is the foundation and a critical need for a multilayered adaptive DDoS defense.
Learn more about NETSCOUT adaptive DDoS protection.