What is an HTTP Flooding DDoS Attack?
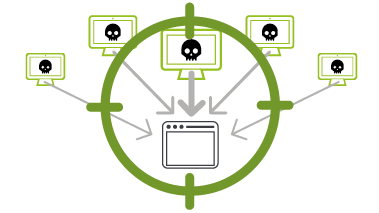
An HTTP flood DDoS attack utilizes what appear to be legitimate HTTP GET or POST requests to attack a web server or application. These application layer DDoS attacks often rely on a botnet, which is a group of Internet-connected computers that have been maliciously appropriated through the use of malware such as a Trojan Horse.

What Are the Signs of an HTTP Flooding DDoS Attack?
These types of DDoS attacks are designed to cause the targeted server or application to allocate the most resources possible in direct response to each request. In this way, the attacker hopes to overwhelm the server or application, “flooding” it with as many process-intensive requests as possible.
HTTP POSTs are often used because they involve complex server-side processing, while HTTP GET attacks are easier to create, thus lending themselves to botnet attacks which rely on scale to achieve the desired disruption.

Why Are HTTP Flooding DDoS Attacks Dangerous?
Because they use standard URL requests, HTTP flooding attacks are nearly indistinguishable from valid traffic. Because they don’t rely on malformed packets, spoofing or reflection techniques, they are difficult to detect. And since they require lower bandwidth than brute force attacks, they can often “fly under the radar” while bringing down a targeted site or server.
HTTP flooding DDoS attacks are specifically designed for the particular target they are aimed at, making them much harder to uncover and block.

How to Mitigate and Prevent an HTTP Flooding DDoS Attack
Since traffic volume in HTTP flooding DDoS attacks is generally below detection thresholds, standard rate-based detection is ineffective at detecting these layer 7 DDoS attacks. A better approach is a combination of traffic profiling techniques, including establishing an IP reputation database so as to track and block abnormal activity, and deploying progressive security challenges. By issuing a requirement such as a JavaScript computational challenge to the requesting machine, it is possible to test if a bot is involved, and thus mitigate an attack if it is.
Additional means of preventing an HTTP flooding DDoS attack include a web application firewall (WAF), as well as constant monitoring by threat engineers.
How can NETSCOUT help?
NETSCOUT's Arbor DDoS solution has been protecting the world's largest and most demanding networks from DDoS attacks for more than a decade. We strongly believe that the best way to protect your resources from modern DDoS attacks is through a multi-layer deployment of purpose-built DDoS mitigation solutions.
Only with a tightly integrated, multi-layer defense can you adequately protect your organization from the full spectrum of DDoS attacks.
Arbor SP/Threat Mitigation System
NETSCOUT customers enjoy a considerable competitive advantage by getting both a micro view of their own network, via our products, combined with a macro view of global Internet traffic, via NETSCOUT Cyber Threat Horizon, an interface to our ATLAS threat intelligence and a DDoS Attack Map visualization.



