A Smarter Network Starts With Smarter Data
Businesses need the right tools to make sense of all of the data that crosses today’s complex and dispersed networks.

Driven by imperatives around digital transformation, the typical enterprise’s network isn’t growing simply in terms of the volume of data it processes—IDC estimates the size of the global datasphere will experience a compound annual growth rate of 23% through 2025—but in complexity, as well. According to a 2020 survey of cybersecurity professionals from the SANS Institute, 93% indicated their organization was managing more than 1,000 endpoints. Nearly 90% said they were managing between hundreds and thousands of servers, and 51% used tools from more than 10 vendors to derive insight into operations.
That growth, driven by multiplying software-as-a-service (SaaS) applications, the rise of remote work, cloud adoption and more, isn’t simply about scale. “Not only are the networks much bigger and more complex, but they’re also changing all the time,” says Paul Barrett, chief technology officer, enterprise at NETSCOUT. “They’re in a state of constant flux. So, that really is one of the biggest challenges we have in monitoring: these very large, very dynamic networks.”
Whether to maximize the efficiency of network operations or protect against cyber attacks—objectives that are inexorably linked—the ability to see and understand what’s happening on the network is critical. For data to be valuable it must also be visible, providing actionable information allowing companies to target fixes appropriately. Yet while the SANS survey indicates 59% of respondents believe a lack of network visibility poses high or very high risk to operations, companies still don’t see what they should. Fifty-two percent indicated a high degree of north-south visibility (understanding data flowing into and out of the network), and only 17% reported a high visibility into east-west traffic (data flowing within their own networks). A full 46% said they have low, or even no, visibility.
For those companies especially, that visibility gap must be bridged. “There’s no other option; otherwise you’re not able to manage your network,” says Goutham Belliappa, vice president of cognitive, AI and big data practice at Capgemini. “You have to ask questions, as well. How comprehensive is that visibility? How integrated is it into automated operations? Into automated anomaly detection?”
Not Just Data, But the Right Data
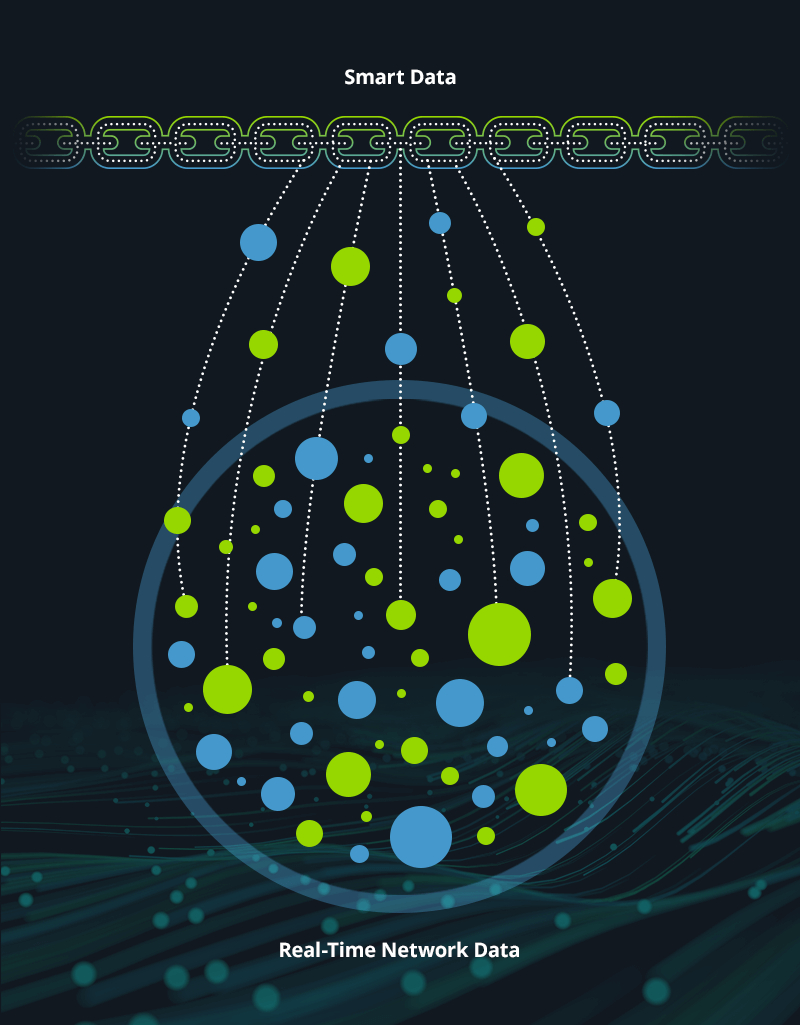
Effective monitoring, Barrett says, requires robust analytics capable of detecting anomalous activity among more typical patterns. NETSCOUT has decades of experience managing the vast quantities of data created by modern networks. Its Smart Data technology, Barrett says, is able to separate signal from noise in anomaly detection by generating usable metadata—essentially, data providing information about other data—from every packet of data that crosses the network. “Our metadata is much more compact and has natural indexing built into it,” Barrett says. “It provides data in much smaller quantities that enterprises can actually handle, allowing it to be analyzed, organized and visualized.”
We have to adopt a ‘shift left’ mentality associated with operations, looking at things through a security lens to see if it’s a security problem first, because if it is we want to stop that as quickly as possible.Paul Barrett, Chief Technology Officer, Enterprise, NETSCOUT
Moreover, in modern networks, different endpoints and systems can generate data with distinct characteristics. Sorting through those differences is critical, so that network operations teams “achieve homogeneous visibility, where the data in all of these locations can be brought together and seen through a single pane of glass,” Barrett says. “You don’t want different types of data from different locations.” Smart Data provides an integrated view of information, no matter where on the network it originates, making the aggregation of data across the organization much simpler.
And because in the first moments of detection it can be difficult to distinguish disruptions related to ordinary network operations from something more nefarious, professionals need tools capable of framing those anomalies in time and place.
In short, context matters.
“With security, companies may not fully understand that they have an incident until some time after the initial penetration occurred,” Barrett notes. “If I’ve got this record of what happened on the network, it’s relatively easy to go back and find that point in time where the attacker made it in. I can see where else they’ve spread on the network—what we call lateral movement—what confidential data if any was accessed or exfiltrated and can quickly make sure any infection is dealt with. With this level of highly contextual data, I can also identify vulnerabilities that were exploited, fix them and use the results of my investigation to influence my remediation efforts.”
The Right Kind of Collaboration
For companies to most successfully leverage the insights gleaned from this type of comprehensive visibility, Belliappa believes they must rethink some of the organizational structures that frequently hinder efficient responses to potential disruptions. “We see companies have issues because they have many security stacks and many different operations that don’t talk to each other. They miss things because you may have an alarm in a silo, but don’t understand its implication for something in another silo,” he says. “Integration and cooperation between operations and security is the only thing that will help them move forward. They all need data visibility. The only question is whether they’re going to do their own little visibility silos or really leverage the scale of the enterprise.”
Barrett agrees. “They have to be intertwined,” he says. “We have to adopt a ‘shift left’ mentality associated with operations, looking at things through a security lens to see if it’s a security problem first, because if it is we want to stop that as quickly as possible. If it’s a performance problem, we’ll hand it over to the network guys to drill down on their level of expertise. So they have to come together.”
When those functions of network operations and security work harmoniously, Barrett believes, there are tremendous benefits to be had across the organization. For starters, highly reliable systems that function as intended create a better employee experience. “We are here to support the business,” he says. “You have to think of it from the perspective of making lives better. How am I providing a better and more secure experience?” Better user experience promotes a higher quality, more consistent customer experience, as well. Meanwhile, customers will trust companies providing reliable services while demonstrating the ability to keep data secure.
Ultimately, technology partners play a key role in providing companies the requisite visibility and intelligence into their networks. The right ones help the enterprise stay focused on core competencies and strategic goals. “They can focus on customer experience and revenue improvement over internal operations, troubleshooting and firefighting,” Belliappa says. “Efficient, secure operations let them focus on growth.”
- - -
This article was written and produced in partnership with the Wall Street Journal. Wall Street Journal Custom Content is a unit of The Wall Street Journal Advertising Department. The Wall Street Journal news organization was not involved in the creation of this content.