About 3 months ago, the Internet experienced the largest DDoS attack ever, reaching the unprecedented level of 1.7 Tbps. This was shortly followed by another attack reaching 1.3 Tbps and numerous smaller attacks. These attacks were based on taking advantage of unsecured Memcached installations around the world, using them as unsuspecting tools in DDoS Reflection type attacks.
But what has happened in the last 3 months after the initial wave of publicity?
Based on publicly available information on Memcached installations worldwide, then at the end of February 2018, there were around 50,000 unsecured Memcached installations on the Internet that could be used as DDoS Reflectors. In the weeks following the large attacks, this number dropped very quickly down to 20,000 and has since then gradually declined down to around 3,500 installations.
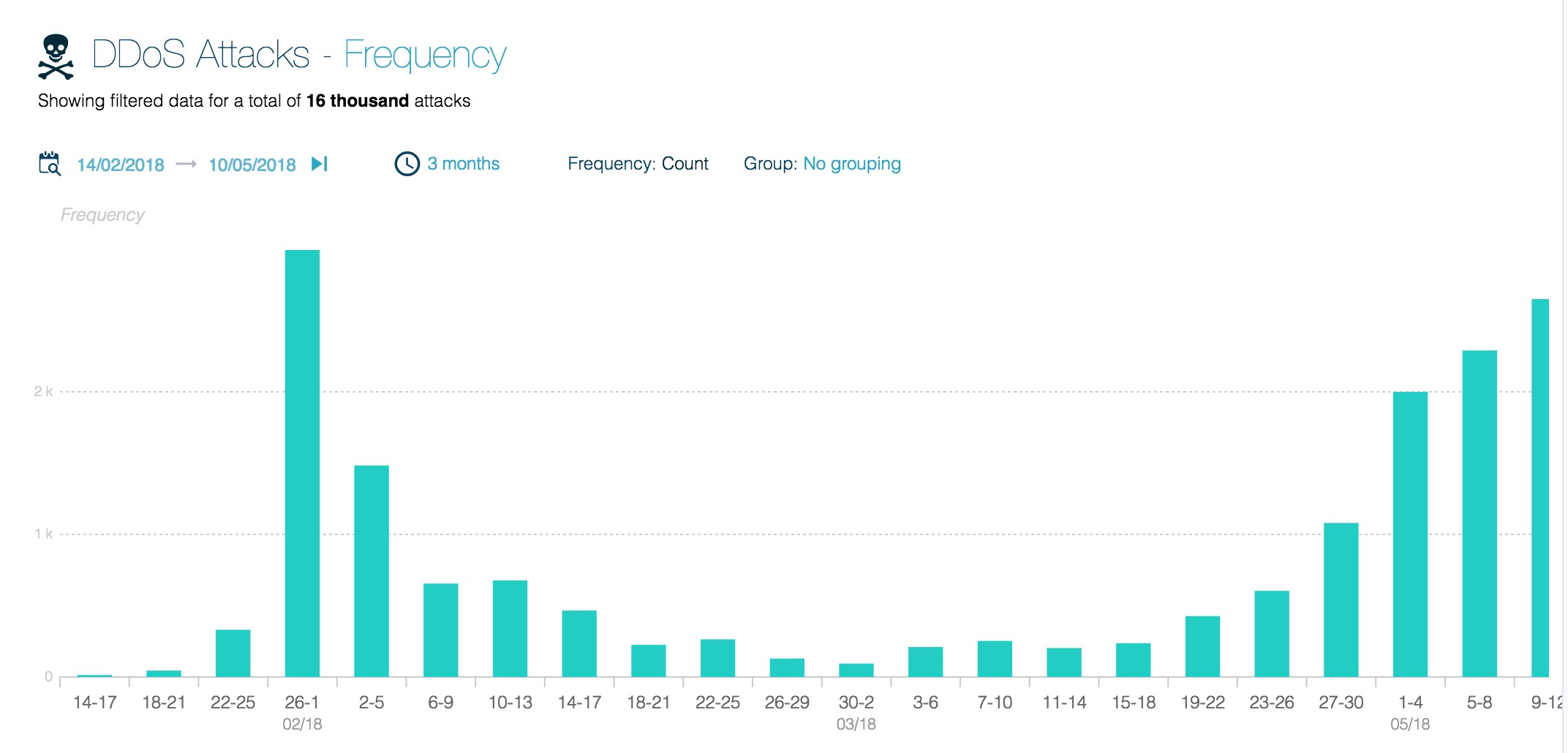
Looking at ATLAS data on Memcached attacks for the same 3-month period, the attack frequency dropped dramatically until around the beginning of April where it began to increase. At the end of April, the attack frequency increased, reaching almost the same levels in mid-May as they were back in February. Digging further into the data, the main reason for this apparent increase is because ATLAS began to receive attack statistics from Arbor customers in the Asia, Africa, and Europe regions, increasing the total visibility into the global DDoS traffic. Taking this increase into consideration, the attack frequency has remained flat since March.
This demonstrates that even while the number of vulnerable services decrease and customers are more aware of Memcached threat vector, the attackers adapt accordingly and have managed to weaponize Memcached as an attack tool.
- The initial attacks were launched by skilled attackers which had done the research necessary to identify a new DDoS reflection vector and how to take advantage of it. After the initial attacks, the attack volume decreased as the attackers had proven their point and the number of vulnerable systems around the world were secured.
- In early April, a proof-of-concept attack tool using Memcached was released on Github, making it easy for anyone to launch these kinds of attacks.
- By late April, the Booter/Stresser community began offering Memcached as an attack vector, effectively weaponizing Memcached and making it easy to use as an attack tool for anyone. These attacks were done using both vulnerable services on the Internet and but also using their own pre-deployed vulnerable installations.
- As Memcached is such an effective DDoS reflector (can reach amplification levels up to 1:500,000), the Booter/Stresser community doesn’t have to rely on finding and taking advantage of unsecure installations. They can simply deploy their own vulnerable servers around the world at various Hosting Providers, paying with stolen credit cards or using one of the various Crypto Currencies. These servers can then be used as Memcached DDoS reflectors until the Hosting Provider detects the abuse of their services and takes the servers down.
This demonstrates that the time from the discovery of a new attack vector to a full-scale weaponization of the attack, can be very short, in this case less than 3 months. Memcached has now become just another attack vector for DDoS attacks, just like DNS, NTP, SSDP and numerous other actively used attack vectors.
New attack vectors will certainly appear in the future as the attackers are always looking for new vulnerabilities, both in existing solutions but also in new services and technologies.
As explained in the ASERT blog on Memcached, published February 27th 2018, detecting and mitigating Memcached attacks is matter of implementing Security Best Practices and deploying Intelligent DDoS Mitigation Systems (IDMS) such as Arbor SP/TMS and Arbor APS where appropriate. Rate-limiting inbound traffic on UDP/TCP port 11211 (and outbound traffic where appropriate) has also been shown to be highly effective in limiting the impact of such attacks.
